48 Secure Shell Ssh Protocol Its Working Cns

Secure Shell Protocol Ssh Protocol Home Page Iotedu #48 secure shell (ssh) protocol & its working |cns| trouble free 215k subscribers 1.9k. #1 introduction & need for security cryptography, information security #2 security approaches and principles or goals of security cryptography |information security| #3 types of security attacks active & passive attacks and their types |information security| #4 security services in network security | information security | #5 security mechanisms in network security | information security | #6 model for network security | information security | #7 basics of network security, important terminologies | information security | #8 encryption techniques substitution & transposition techniques |information security| #9 monoalphabetic ciphers & polyalphabetic ciphers encryption techniques | information security | #10 caesar cipher with example encryption technique | information security | #11 playfair cipher with example encryption techniques | information technology | #12 hill cipher with example encryption techniques | information security | #13 one time pad vernam cipher with example encryption techniques | information security | #14 rail fence & columnar transposition with example encryption techniques|information security| #15 symmetric & asymmetric key cryptography with diagram |information security| #16 concept of steganography in network security |information security| #17 block cipher introduction & design principles of block cipher |information security| #18 data encryption standard ( des ) algorithm |cns| #19 advanced encryption standard ( aes ) algorithm block cipher algorithm |cns| #20 blowfish algorithm block cipher algorithm |cns| #21 idea ( international data encryption algorithm ) block cipher algorithm |cns| #22 block cipher modes of operation part 1 |cns| #23 block cipher modes of operation part 2 |cns| #24 stream cipher working with example |cns| #25 rc4 algorithm block cipher algorithm |cns| #26 symmetric key distribution methods |cns| #28.
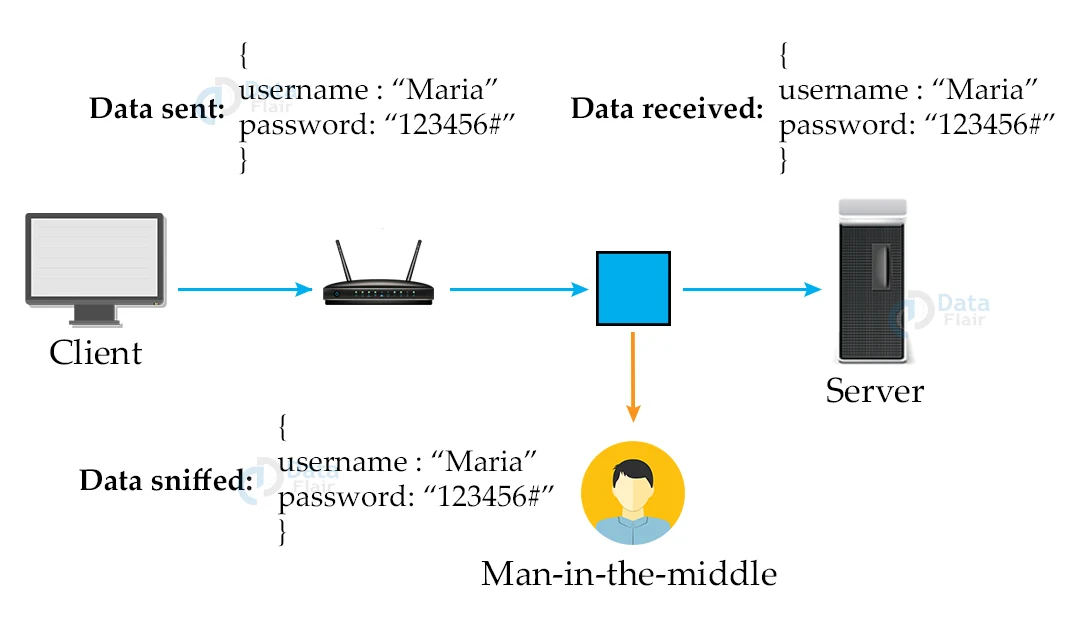
Ssh Protocol Secure Shell Dataflair Secure shell (ssh) is a cryptographic network protocol used for secure remote access and file transfer over a network. ssh1 was the first version of the secure shell protocol, released in 1996. Secure shell (ssh) is a protocol for secure network communications designed to be relatively simple and inexpensive to implement. the initial version, ssh1 was focused on providing a secure remote logon facility to replace telnet and other remote logon schemes that provided no security. In this article, we will discuss the overview of ssh (secure shell) protocol and then will mainly focus on its architecture part and will explain its working. let's discuss it one by one. Pay attention to the “hostkeyalgorithms” setting in etc ssh ssh config to help determine this order or use ssh command line switches to override these settings.
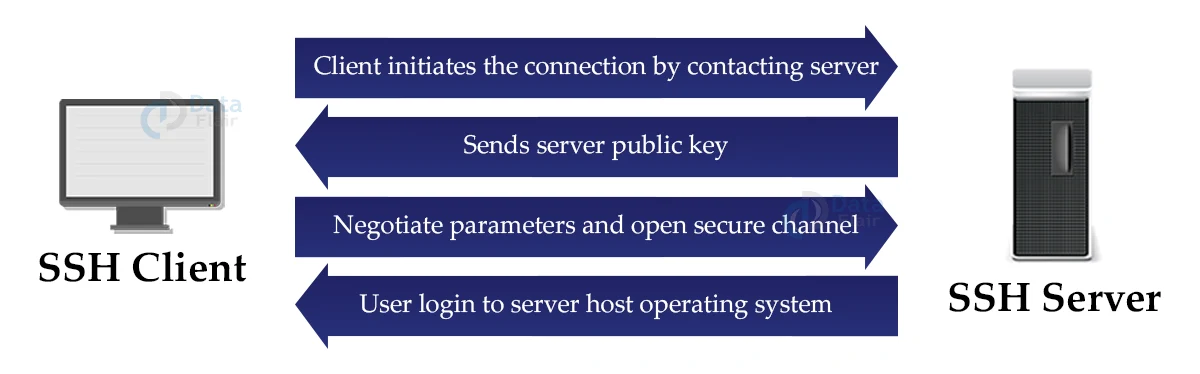
Ssh Protocol Secure Shell Dataflair In this article, we will discuss the overview of ssh (secure shell) protocol and then will mainly focus on its architecture part and will explain its working. let's discuss it one by one. Pay attention to the “hostkeyalgorithms” setting in etc ssh ssh config to help determine this order or use ssh command line switches to override these settings. This protocol allows the server and client to authenticate each other and to negotiate an encryption and mac algorithm and cryptographic keys to be used to protect data sent in an ssl record. Abstract the secure shell (ssh) is a protocol for secure remote login and other secure network services over an insecure network. this document describes the ssh transport layer protocol, which typically runs on top of tcp ip. the protocol can be used as a basis for a number of secure network services. it provides strong. The secure shell protocol (ssh protocol) is a cryptographic network protocol for operating network services securely over an unsecured network. [1] its most notable applications are remote login and command line execution. This document specifies the conventions for using the united states national security agency's cnsa suite algorithms with the secure shell transport layer protocol and the secure shell authentication protocol.
Comments are closed.