403 Bypass Github Topics Github
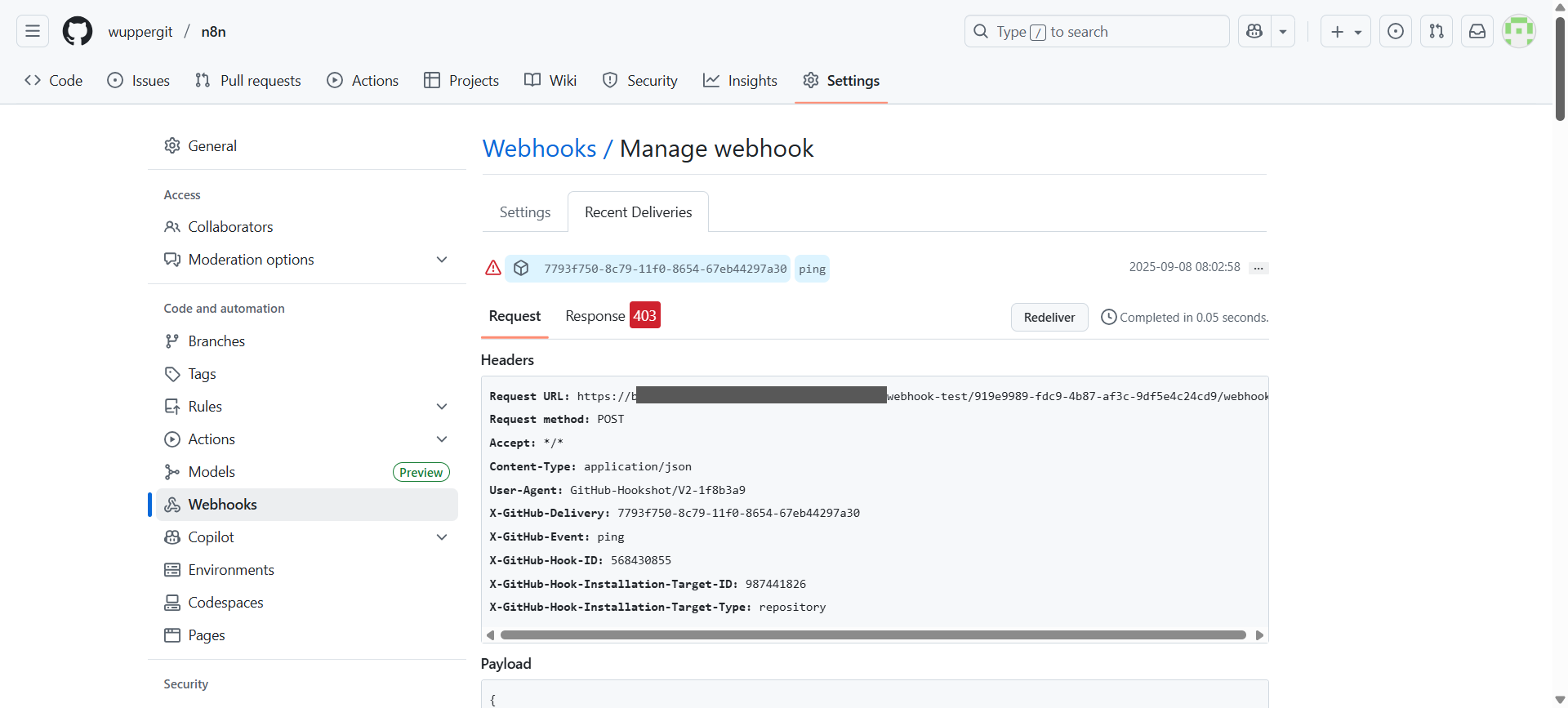
Github Trigger Response 403 Questions N8n Community Using this tool, you can fuzz your 403 401 endpoint and try to access it without any restrictions. you can also customize your payloads and update them regularly. Interactive cheat sheet of security tools collected from public repos to be used in penetration testing or red teaming exercises.
Github 限制国内访问 别慌 完美解决方案来了 腾讯云开发者社区 腾讯云 Automate critical tasks and eliminate the need to move data externally. download now. note: the open source projects on this list are ordered by number of github stars. the number of mentions indicates repo mentiontions in the last 12 months or since we started tracking (dec 2020). 4 zero 3 is a free and open source tool available on github. it's a bash script.4 zero 3 is used to bypass 403 and 401 technical obstacles on any domain. content length matters when performing bypass using the 4 zero 3 tool. I've published the tool i use to bypass http 403 error pages and access the juicy information behind 👀. it is written in golang, it's very fast, and it incorporates many techniques from book.hacktricks. Please consider following and supporting us to stay updated with the latest info.
403 Bypass Github Topics Github I've published the tool i use to bypass http 403 error pages and access the juicy information behind 👀. it is written in golang, it's very fast, and it incorporates many techniques from book.hacktricks. Please consider following and supporting us to stay updated with the latest info. The http 403 status code indicates that access to a requested resource is forbidden. while this is a security measure, misconfigurations in web applications often allow attackers to bypass. Hello hackers, today in this write up i am going to give you all things you need to know to bypass 403 & 401 error page, some automation tools, tips and tricks, medium articles, hackerone disclosed reports all the thing so let’s get started. A tool designed to automate various techniques in order to bypass http 401 and 403 response codes and gain access to unauthorized areas in the system. this code is made for security enthusiasts and professionals only. 🔓 bypassx an interactive security lab for testing and learning 403 bypass techniques. features 60 protected endpoints with real world scenarios to master web application security bypass methods.

403 Bypass Github Topics Github The http 403 status code indicates that access to a requested resource is forbidden. while this is a security measure, misconfigurations in web applications often allow attackers to bypass. Hello hackers, today in this write up i am going to give you all things you need to know to bypass 403 & 401 error page, some automation tools, tips and tricks, medium articles, hackerone disclosed reports all the thing so let’s get started. A tool designed to automate various techniques in order to bypass http 401 and 403 response codes and gain access to unauthorized areas in the system. this code is made for security enthusiasts and professionals only. 🔓 bypassx an interactive security lab for testing and learning 403 bypass techniques. features 60 protected endpoints with real world scenarios to master web application security bypass methods.

403 Bypass Github Topics Github A tool designed to automate various techniques in order to bypass http 401 and 403 response codes and gain access to unauthorized areas in the system. this code is made for security enthusiasts and professionals only. 🔓 bypassx an interactive security lab for testing and learning 403 bypass techniques. features 60 protected endpoints with real world scenarios to master web application security bypass methods.
Comments are closed.