4 25 19 Stealjob Android Malware Used By Donot Apt Group Att Threattraq

Android Malware In Donot Apt Operations Cyfirma At&t data security analysts stan nurilov, michael klepper and karen simon discuss the week's top cyber security news, and share news on the current trends of malware, spam, and internet anomalies observed on the at&t network. After performing correlation analysis, we suspect that the new apk framework is probably used by donot. although the code structure of the program is quite different when comparing with the one used in aug, 2018, the c&c style still remains the same.

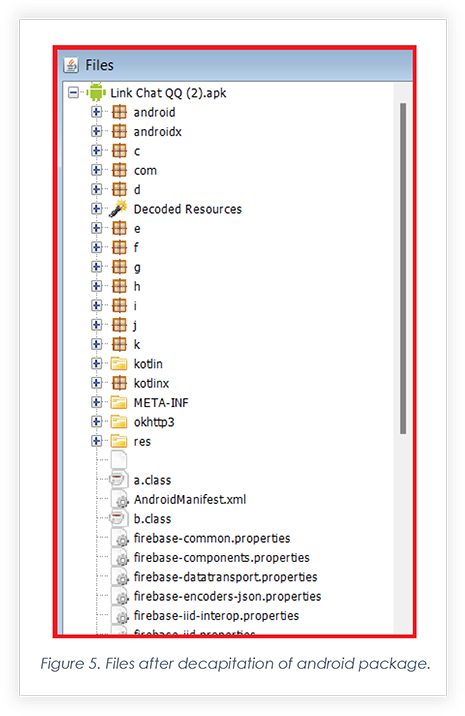
Donot Apt Targets Individuals In South Asia Using Android Malware Cyfirma Go.att 4f2fb685originally recorded on april 23, 2019at&t threattraq welcomes your e mail questions and feedback at [email protected] at&. Recently, we have observed a large scale upgrade of its malicious android apk framework to make it more stable and practical. since the new apk framework is quite different from the one used in the past, we named it as stealjob since “job” is frequently used in the code. Researchers linked the threat actor donot team to a new android malware that was employed in highly targeted cyber attacks. cyfirma researchers linked a recently discovered android malware to the indian apt group known as donot team. The cybersecurity community is well aware that the donot group is actively targeting organizations and individuals across the south asia region. the group persistently employs similar techniques in their android malware.
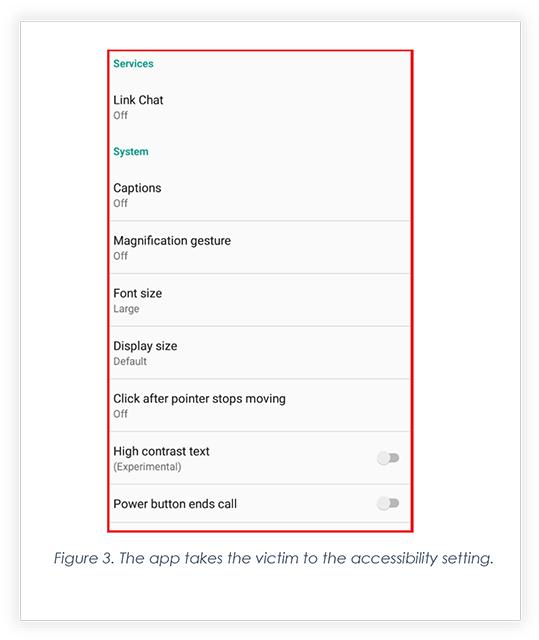
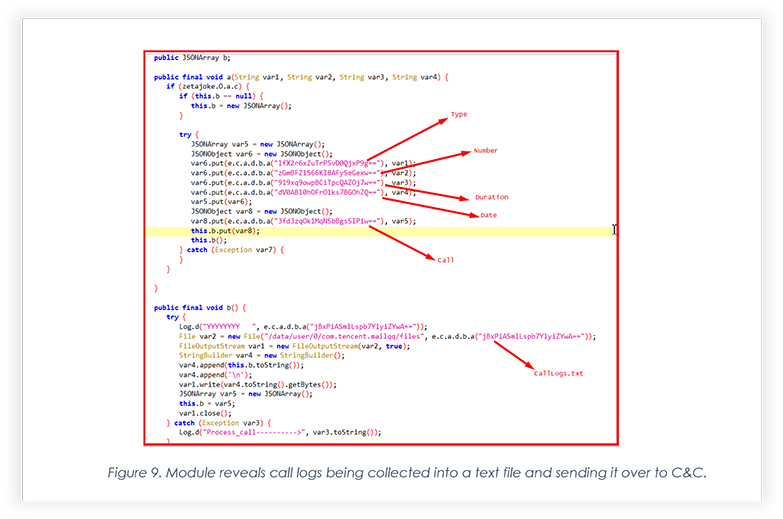
Donot Apt Targets Individuals In South Asia Using Android Malware Cyfirma Researchers linked the threat actor donot team to a new android malware that was employed in highly targeted cyber attacks. cyfirma researchers linked a recently discovered android malware to the indian apt group known as donot team. The cybersecurity community is well aware that the donot group is actively targeting organizations and individuals across the south asia region. the group persistently employs similar techniques in their android malware. A recent publication by cyfirma highlighted a sophisticated android malware campaign linked to the donot advanced persistent threat (apt) group. the attackers use malicious apps and domains to distribute spyware capable of stealing sensitive user information and gaining unauthorized access to devices. Donot has been actively dropping malicious android apk sample and targeting android users to exfiltrate data. the group has previously been active in the past and has now again shifted its focus to android malware. In addition to malicious documents, the group also appears to have android malware, such as android rat malware found as a rogue kashmir news service lite app and more like that. the group’s android malware disguises itself in two different ways. fake app icons and error messages. The donot apt (aka apt c 35) has been active since 2016. they have attacked many individuals and organisations in south asia. donot apt is reported to be the main developers and users of frameworks for developing windows and android malware [1].
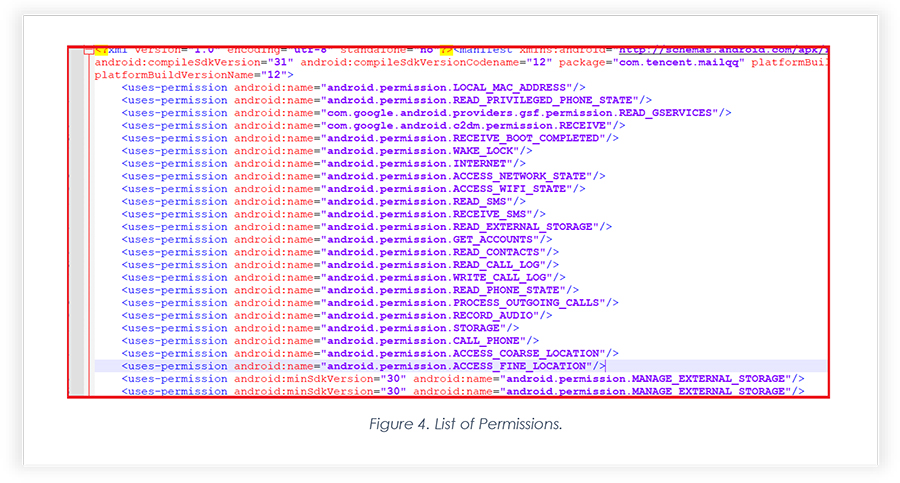
Donot Apt Targets Individuals In South Asia Using Android Malware Cyfirma A recent publication by cyfirma highlighted a sophisticated android malware campaign linked to the donot advanced persistent threat (apt) group. the attackers use malicious apps and domains to distribute spyware capable of stealing sensitive user information and gaining unauthorized access to devices. Donot has been actively dropping malicious android apk sample and targeting android users to exfiltrate data. the group has previously been active in the past and has now again shifted its focus to android malware. In addition to malicious documents, the group also appears to have android malware, such as android rat malware found as a rogue kashmir news service lite app and more like that. the group’s android malware disguises itself in two different ways. fake app icons and error messages. The donot apt (aka apt c 35) has been active since 2016. they have attacked many individuals and organisations in south asia. donot apt is reported to be the main developers and users of frameworks for developing windows and android malware [1].
Donot Apt Targets Individuals In South Asia Using Android Malware Cyfirma In addition to malicious documents, the group also appears to have android malware, such as android rat malware found as a rogue kashmir news service lite app and more like that. the group’s android malware disguises itself in two different ways. fake app icons and error messages. The donot apt (aka apt c 35) has been active since 2016. they have attacked many individuals and organisations in south asia. donot apt is reported to be the main developers and users of frameworks for developing windows and android malware [1].
Donot Apt Targets Individuals In South Asia Using Android Malware Cyfirma
Comments are closed.