35k Lines Of Malware In Github

Gitvenom Campaign Steals Crypto Via Github Cybernews Hackers are exploiting anthropic's accidental claude code source leak to distribute vidar and ghostsocks malware through fake github repositories. the campaign targets developers searching for the. Malicious github repository using the leaked claude code source as a lure (source: zscaler) delivering vidar and ghostsocks malware in this newly discovered campaign, attackers have established malicious github repositories that masquerade as the authentic leaked repository.
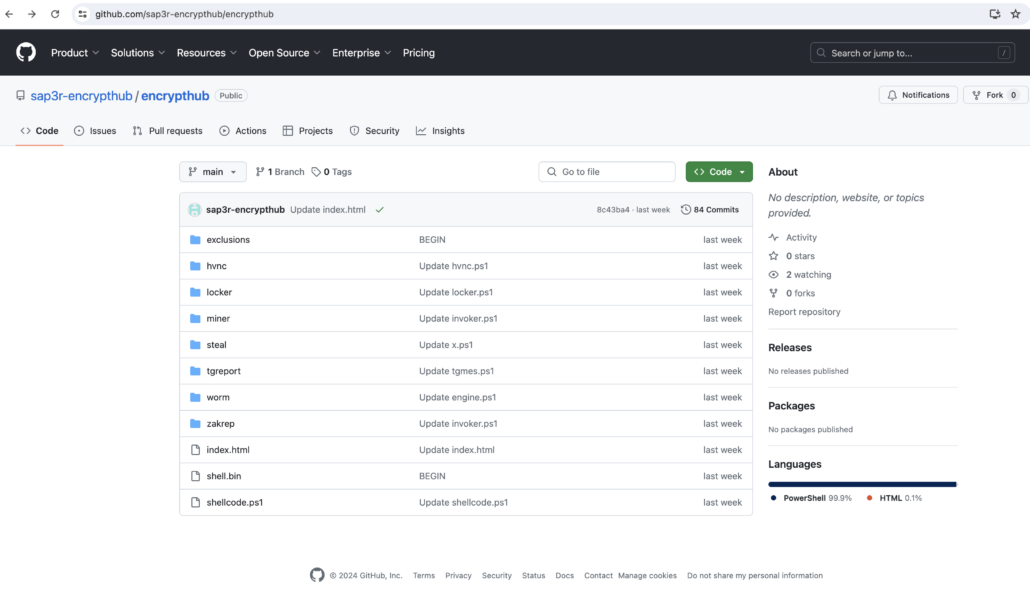
Beware Of Fake Winrar Websites Malware Hosted On Github Collection of malware source code for a variety of platforms in an array of different programming languages. Breaking (april 4, 2026) on march 31, 2026, anthropic accidentally shipped the complete source code for claude code inside a public npm package. within hours, 512,000 lines of typescript were mirrored across github, a critical vulnerability was discovered, and malware campaigns began targeting developers. this post covers everything that happened, what it means for your security, and exactly. Premium quality tank top made of 100% cotton (heather gray is 95% cotton 5% viscose, charcoal gray is 80% cotton 20% polyester). twitter stephenlacy status 1554697077430505473uncle. In the wake of a significant source code leak for anthropic's claude code tool, a new and immediate threat has emerged. cybercriminals have swiftly weaponized the incident, creating deceptive github repositories that promise the leaked code but instead deliver dangerous information stealing malware. this rapid exploitation highlights the persistent security risks that accompany high profile.

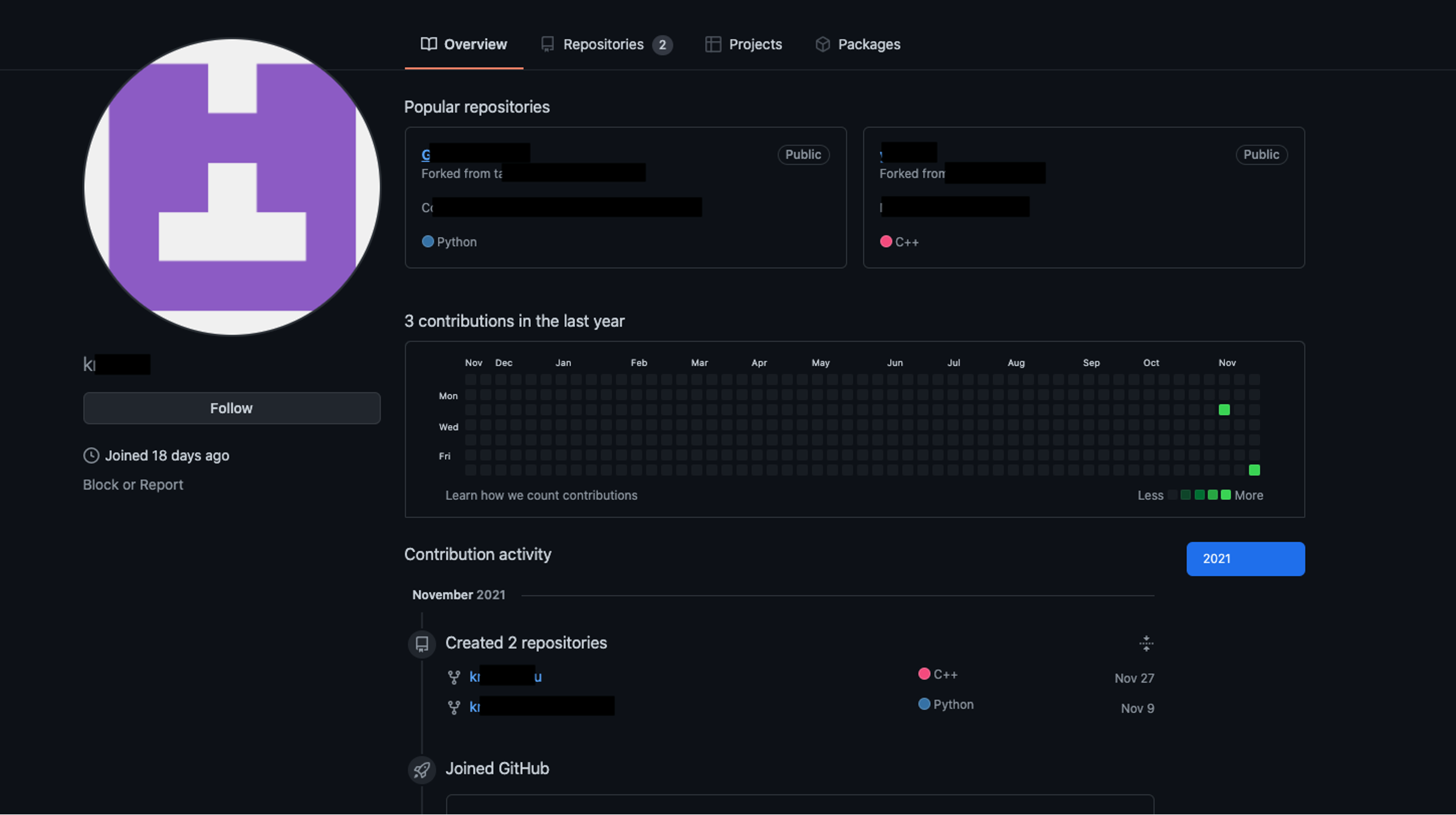
Github Users Targeted With Dangerous Malware Attacks Here S What We Premium quality tank top made of 100% cotton (heather gray is 95% cotton 5% viscose, charcoal gray is 80% cotton 20% polyester). twitter stephenlacy status 1554697077430505473uncle. In the wake of a significant source code leak for anthropic's claude code tool, a new and immediate threat has emerged. cybercriminals have swiftly weaponized the incident, creating deceptive github repositories that promise the leaked code but instead deliver dangerous information stealing malware. this rapid exploitation highlights the persistent security risks that accompany high profile. With anthropic rushing to wipe out the claude code leak, hackers are posting malware laden files on github that they claim are special, unlocked versions of the ai tool. According to the tweets shared by github developer stephen lacy, over 35,000 repositories have been infected, including crypto, golang, python, javascript, bash, docker, and kubernetes. Github has devalued the brand of large projects and has introduced the age of industrialized software development by creating an addictive environment where software politicians thrive by manipulating their social networks and working on their personal brand. Cybercriminals are exploiting the recent claude code source code leak to distribute vidar malware via fake github repositories.
How Threat Actors Can Use Github Repositories To Deploy Malware With anthropic rushing to wipe out the claude code leak, hackers are posting malware laden files on github that they claim are special, unlocked versions of the ai tool. According to the tweets shared by github developer stephen lacy, over 35,000 repositories have been infected, including crypto, golang, python, javascript, bash, docker, and kubernetes. Github has devalued the brand of large projects and has introduced the age of industrialized software development by creating an addictive environment where software politicians thrive by manipulating their social networks and working on their personal brand. Cybercriminals are exploiting the recent claude code source code leak to distribute vidar malware via fake github repositories.
How Threat Actors Can Use Github Repositories To Deploy Malware Github has devalued the brand of large projects and has introduced the age of industrialized software development by creating an addictive environment where software politicians thrive by manipulating their social networks and working on their personal brand. Cybercriminals are exploiting the recent claude code source code leak to distribute vidar malware via fake github repositories.
Comments are closed.