3 Vulnerability Prioritization And Risk Assessment

Risk Prioritization Improving Network Vulnerability Security This paper presents the motivation for cve prioritization for a given case and describes an outline process for evaluating the priority of cves via risk assessment simulations. Vulnerability prioritization is the process of evaluating and ranking discovered security vulnerabilities based on the actual risk they pose to your specific environment, so your team fixes the issues most likely to result in a breach first.

Vulnerability Prioritization Go beyond cvss scores. learn how to prioritize vulnerabilities by exploitability, asset value, and threat intel to focus on real risks and strengthen resilience. Learn essential strategies and expert tips for effective vulnerability prioritization, ensuring your cybersecurity posture is resilient. This work presents frape, a novel risk based vulnerability management (rbvm) framework designed to help analysts classify and prioritize the remediation of security flaws. By encompassing multiple dimensions of vulnerability prioritization, the taxonomy addresses the complexities of contemporary cybersecurity challenges, including regulatory pressures, the growing volume of vulnerabilities, and the need for holistic risk assessment frameworks.
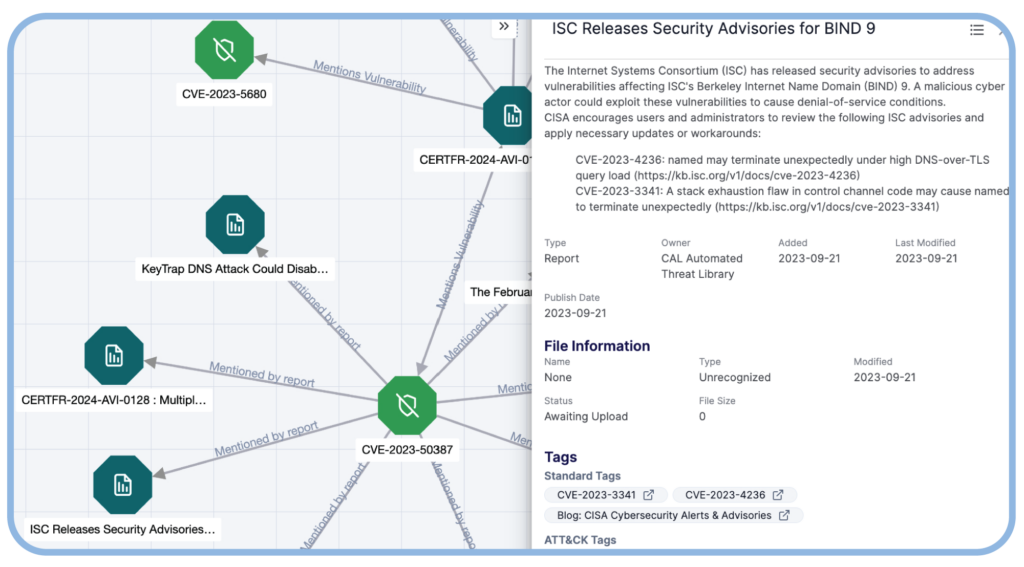
Vulnerability Prioritization Vulnerability Prioritization Tool This work presents frape, a novel risk based vulnerability management (rbvm) framework designed to help analysts classify and prioritize the remediation of security flaws. By encompassing multiple dimensions of vulnerability prioritization, the taxonomy addresses the complexities of contemporary cybersecurity challenges, including regulatory pressures, the growing volume of vulnerabilities, and the need for holistic risk assessment frameworks. This article dives into the concept of vulnerability prioritization, explores the role of risk assessment, highlights various tools and techniques, and presents a real life case study. Modern cybersecurity demands a sophisticated approach to vulnerability management. this guide explains why industry leaders have moved beyond simple cvss scoring to embrace multi factor risk assessment using cvss, kev, and epss data. Learn how to effectively prioritize vulnerabilities to enhance security, reduce risks, and focus on the most critical threats. Vulnerability prioritization should be based on real world risk. learn how exploitability, business context, and continuous testing outperform cvss alone.

6 Steps To Effective Vulnerability Prioritization Wiznucleus This article dives into the concept of vulnerability prioritization, explores the role of risk assessment, highlights various tools and techniques, and presents a real life case study. Modern cybersecurity demands a sophisticated approach to vulnerability management. this guide explains why industry leaders have moved beyond simple cvss scoring to embrace multi factor risk assessment using cvss, kev, and epss data. Learn how to effectively prioritize vulnerabilities to enhance security, reduce risks, and focus on the most critical threats. Vulnerability prioritization should be based on real world risk. learn how exploitability, business context, and continuous testing outperform cvss alone.
Comments are closed.