2fa Guide Fix Weak Authentication With These Methods Hideez

Hideez Key For Cyberark Authentication Integration Discover what 2fa (two factor authentication) is, why it can fail, and explore the most secure authentication methods for 2024. learn how to avoid common vulnerabilities like phishing and sim swapping. Binance push 2fa (also called binance app verification) is a two factor authentication method where you approve login or withdrawal requests directly inside the binance mobile app 📲.
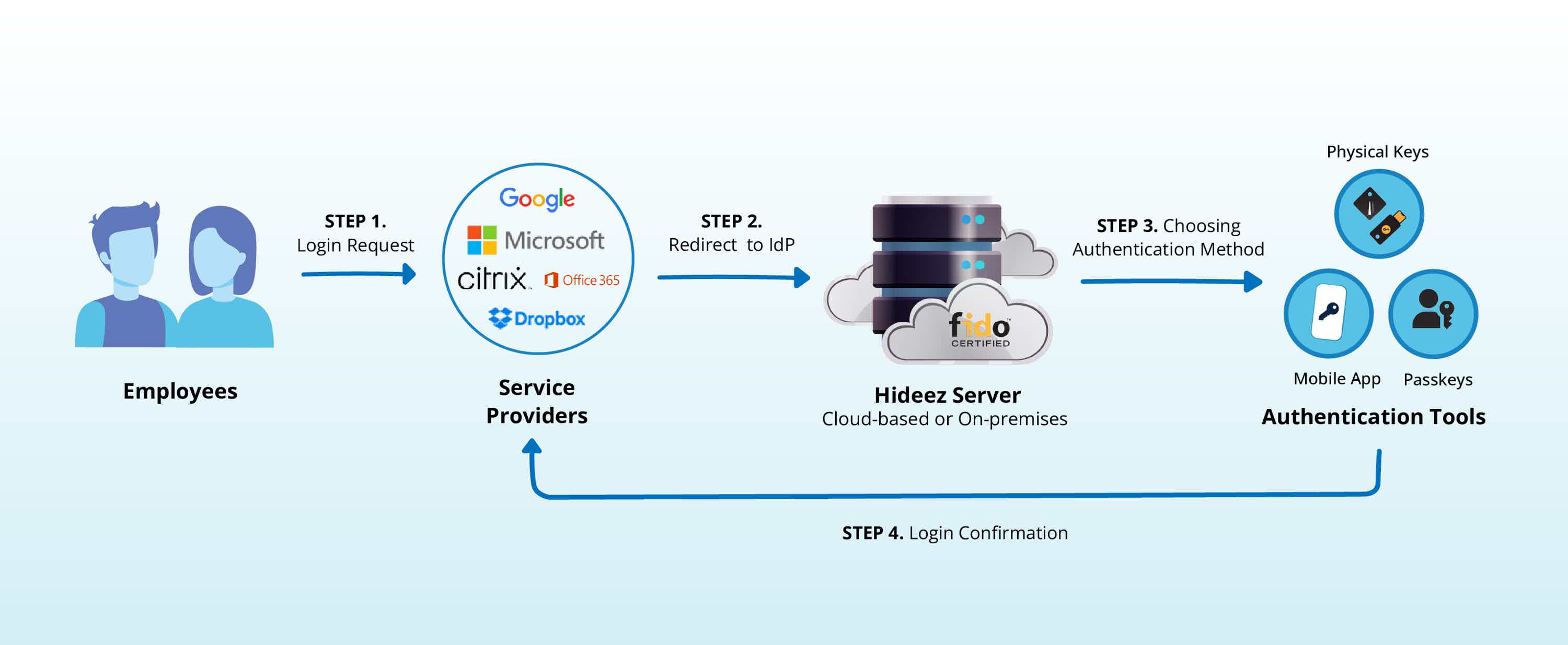
Sso Login To Webservises Fido2 Via Mobile App Hideez Authentication Sometimes the login flow starts 2fa, but other endpoints don’t enforce this check, or client side controls are trusted incorrectly. tokens issued before completing 2fa can be reused to bypass. Two factor authentication (2fa) is widely used to secure accounts, but misconfigurations and flawed implementations often make it bypassable. this repository serves as a comprehensive research hub for identifying, testing, and mitigating 2fa bypass vulnerabilities. Two factor authentication adds an extra layer of security beyond passwords, but attackers continually develop methods to circumvent these protections. this guide explores standard 2fa bypass techniques, including phishing, sim swapping, session hijacking, and push notification abuse. To bypass 2fa, access the subsequent endpoint directly, knowing the path is crucial. if unsuccessful, alter the referrer header to mimic navigation from the 2fa verification page. reutilizing previously used tokens for authentication within an account can be effective.

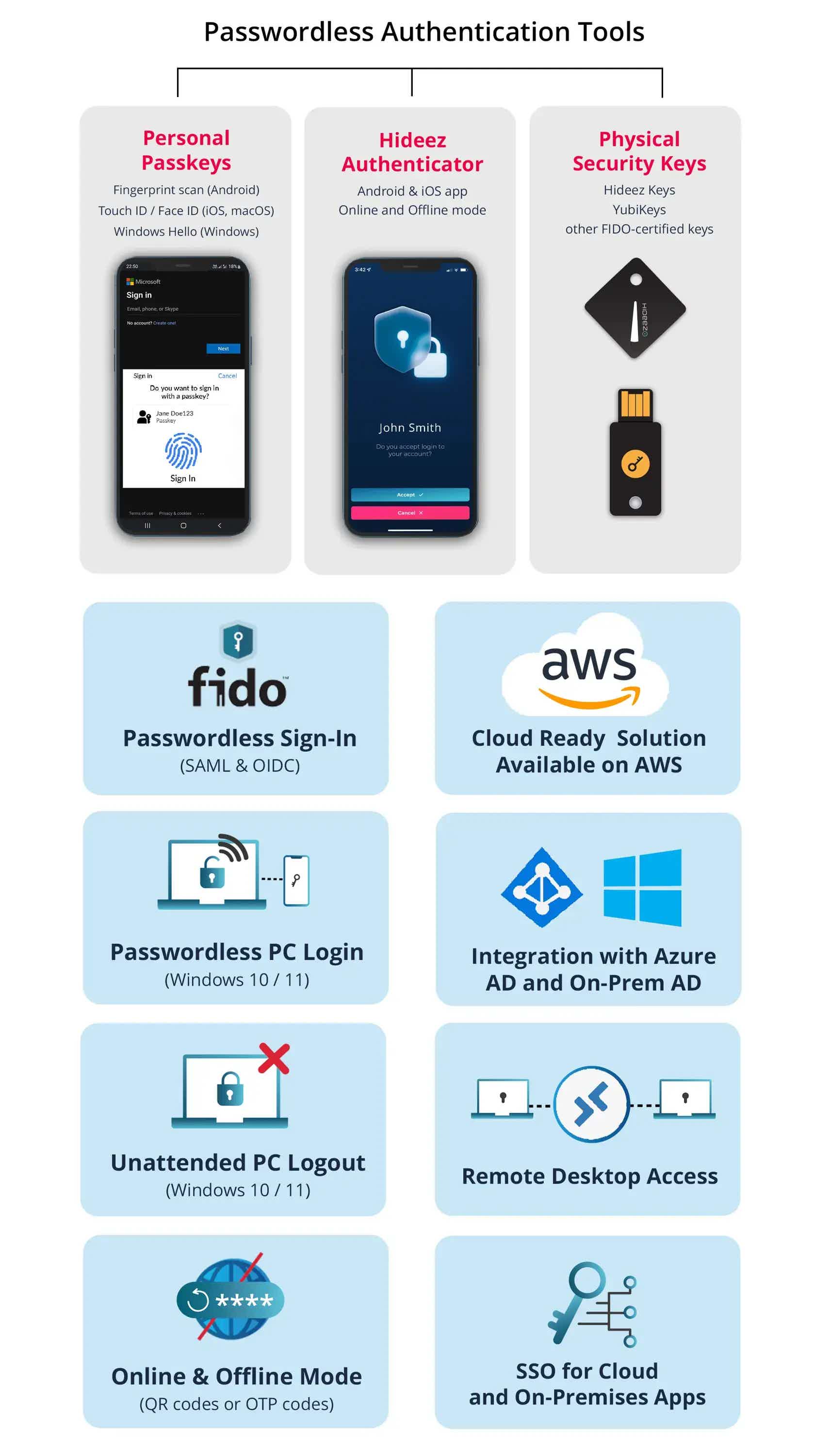
Passwordless Authorization Authentication Solutions Hideez Two factor authentication adds an extra layer of security beyond passwords, but attackers continually develop methods to circumvent these protections. this guide explores standard 2fa bypass techniques, including phishing, sim swapping, session hijacking, and push notification abuse. To bypass 2fa, access the subsequent endpoint directly, knowing the path is crucial. if unsuccessful, alter the referrer header to mimic navigation from the 2fa verification page. reutilizing previously used tokens for authentication within an account can be effective. Learn how attackers bypass two factor authentication, from password reset flaws to ai driven proxy attacks, and discover practical prevention steps to secure your accounts. Multifactor authentication (mfa) or two factor authentication (2fa) is when a user is required to present more than one type of evidence in order to authenticate on a system. Below, we will be exploring several methods on how to exploit 2fa vulnerabilities and take advantage of any present logic flaws in their insecure implementations. For 2fa, attackers have discovered ways to sidestep the stronger protection. whether exploiting human weaknesses or known system vulnerabilities, the effect is similar to kicking a door down to.
Passwordless Workforce Identity Solutions Hideez Learn how attackers bypass two factor authentication, from password reset flaws to ai driven proxy attacks, and discover practical prevention steps to secure your accounts. Multifactor authentication (mfa) or two factor authentication (2fa) is when a user is required to present more than one type of evidence in order to authenticate on a system. Below, we will be exploring several methods on how to exploit 2fa vulnerabilities and take advantage of any present logic flaws in their insecure implementations. For 2fa, attackers have discovered ways to sidestep the stronger protection. whether exploiting human weaknesses or known system vulnerabilities, the effect is similar to kicking a door down to.
Passwordless Workforce Identity Solutions Hideez Below, we will be exploring several methods on how to exploit 2fa vulnerabilities and take advantage of any present logic flaws in their insecure implementations. For 2fa, attackers have discovered ways to sidestep the stronger protection. whether exploiting human weaknesses or known system vulnerabilities, the effect is similar to kicking a door down to.
Comments are closed.