1secure Shell Pdf Secure Shell File Transfer Protocol
Secure Shell Communication Protocol Ssh File Transfer Protocol Network It operates on a client server model, establishing an encrypted connection for executing commands, managing servers, and transferring files securely. the document also provides guidance on setting up ssh on windows, including key management, firewall rules, and using scp and sftp for file transfers. Ssh (secure shell) provides a secure method for logging into remote computers and transferring files. this chapter introduces essential features like remote login and secure file transfer.

Secure Shell Pdf Secure Shell Application Layer Protocols Securefx includes a command line utility for scripting batch jobs to perform secure unattended file transfers using the secure shell protocol (ssh). securefx also supports "relentless" file transfers that automatically reconnect and resume when transfer connections are broken. Defines the logical channels and the requests to handle the services like: secure interactive shell session, tcp port forwarding and x11 forwarding. Through secure authentication and encryption technologies, ssh supports secure remote logins, secure remote command execution, secure file transfers, access control, tcp ip port forwarding, and other important features. Encrypting protocols which are not normally encrypted (e.g. vnc). no setup – already done! the screen display shows up on your computer, and any keystrokes and mouse movements are sent back, all encrypted.

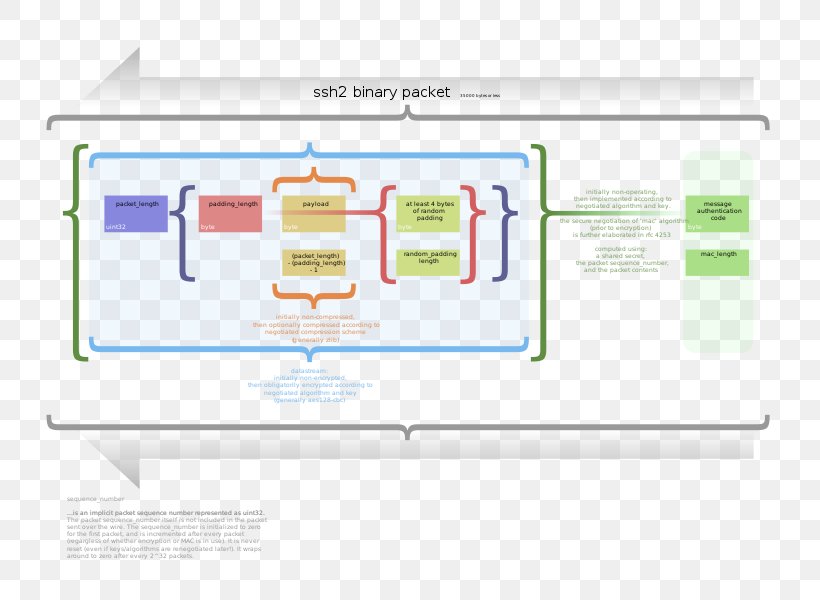
Secure Shell Pdf Secure Shell Computing Through secure authentication and encryption technologies, ssh supports secure remote logins, secure remote command execution, secure file transfers, access control, tcp ip port forwarding, and other important features. Encrypting protocols which are not normally encrypted (e.g. vnc). no setup – already done! the screen display shows up on your computer, and any keystrokes and mouse movements are sent back, all encrypted. Ssh is used as the foundation of the secure copy (scp) and secure file transfer protocol (sftp) protocols. these protocols are used to transfer files between hosts while leveraging the security capabilities built into ssh. Abstract the secure shell (ssh) is a protocol for secure remote login and other secure network services over an insecure network. this document describes the ssh transport layer protocol, which typically runs on top of tcp ip. the protocol can be used as a basis for a number of secure network services. it provides strong. Ssh, standing for secure shell, transformed the landscape of remote access. it provides a secure channel over an unsecured network, protecting your data from eavesdropping and tampering. Ssh also provides a more general client server capability and can be used to secure such network functions as file transfer and e mail. a new version, ssh2, provides a standardized definition of ssh and improves on ssh1 in numerous ways.
Comments are closed.