11 Remote Desktop Access Best Practices

Remote Access Security Best Practices Upd Ev Pdf Even a single overlooked setting can give attackers the opening they need. in this blog, we’ll explore the common risks of remote desktop access and share practical best practices to help you work remotely safely and securely. To maintain secure rdp access in 2025, it’s essential to follow proven rdp security best practices and leverage powerful tools and strategies. in this comprehensive rdp security guide, you’ll discover the most effective ways to secure your rdp sessions, prevent unauthorized access, and reduce rdp vulnerabilities—whether you’re working.

Best Practices For Remote Desktop Access Empower Information Systems Discover 11 proven ways to secure remote desktop access with rdp mfa, encryption, session timeouts, and access controls. In this article, we’ll explore the concept of remote access security, examine real world sector specific examples, assess the benefits and risks, highlight common challenges organizations face, and offer best practices for securing remote access. Secure remote access best practices fall into several broad categories: authentication and access controls, device and network security, data protection and monitoring, user training and audits. To enhance your rdp security, several best practices can be employed to protect your remote environment. testing configurations in a lab environment before implementation is crucial to prevent potential damage in production.
Best Practices For Remote Desktop Access Xterra Solutions Secure remote access best practices fall into several broad categories: authentication and access controls, device and network security, data protection and monitoring, user training and audits. To enhance your rdp security, several best practices can be employed to protect your remote environment. testing configurations in a lab environment before implementation is crucial to prevent potential damage in production. Learn how to secure rdp with vpn, strong passwords, mfa, and network level authentication. protect remote desktop connections from cyberattacks. Secure remote access refers to the methods, technologies, and policies used to protect data and resources when accessing a network or system from a remote location. it ensures that only authorized users can connect and that their data is protected from unauthorized access or interception. Enable remote desktop on windows in minutes—this guide walks you through the exact settings to turn it on and connect securely from anywhere. Securely configure remote support tools (rdp, teamviewer, anydesk): auth, encryption, least privilege, session handling, and audit best practices.
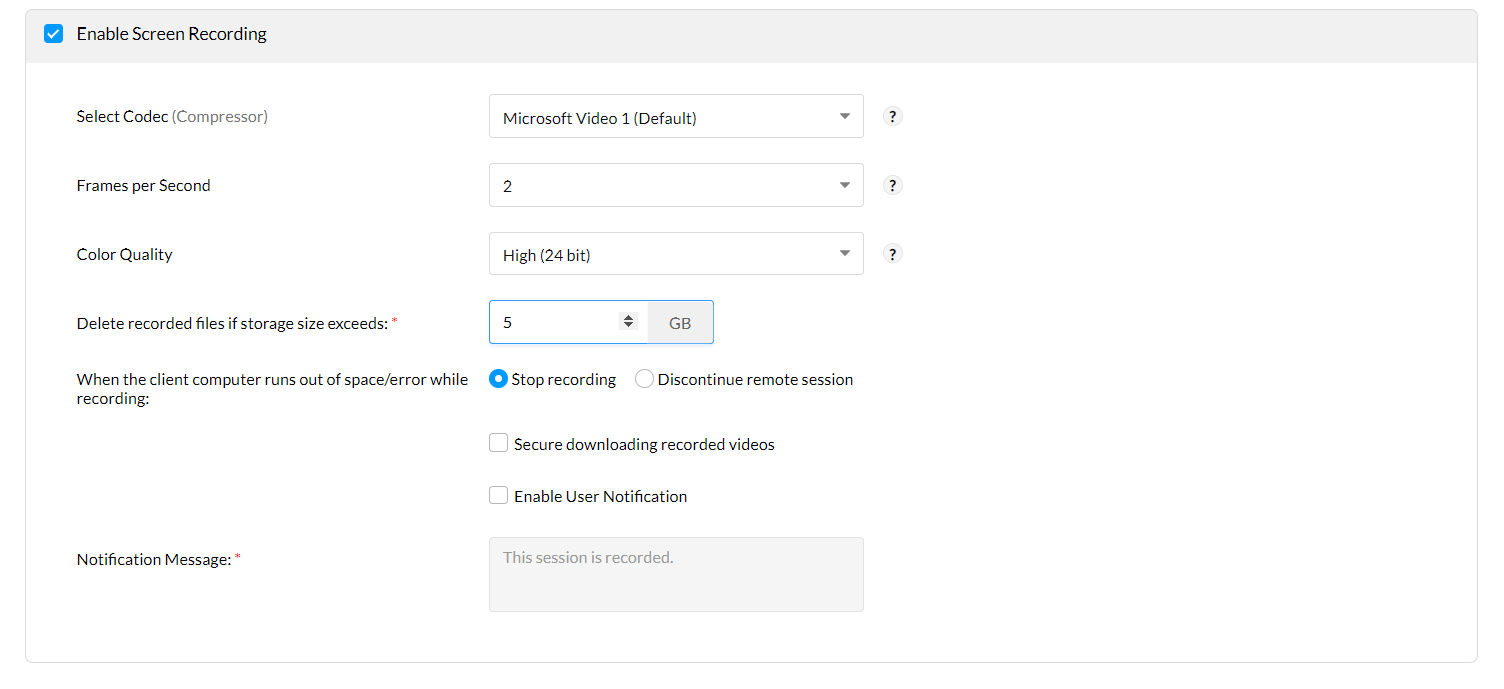
Top 10 Remote Desktop Best Practices Manageengine Remote Access Plus Learn how to secure rdp with vpn, strong passwords, mfa, and network level authentication. protect remote desktop connections from cyberattacks. Secure remote access refers to the methods, technologies, and policies used to protect data and resources when accessing a network or system from a remote location. it ensures that only authorized users can connect and that their data is protected from unauthorized access or interception. Enable remote desktop on windows in minutes—this guide walks you through the exact settings to turn it on and connect securely from anywhere. Securely configure remote support tools (rdp, teamviewer, anydesk): auth, encryption, least privilege, session handling, and audit best practices.
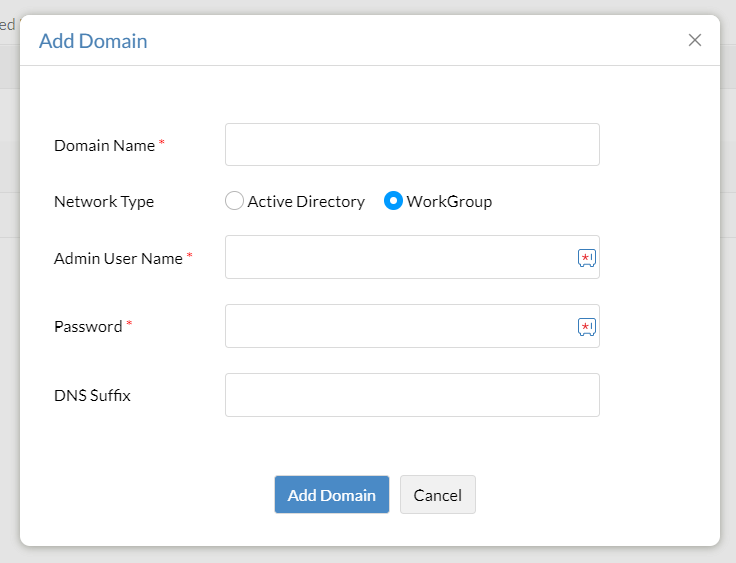
Top 10 Remote Desktop Best Practices Manageengine Remote Access Plus Enable remote desktop on windows in minutes—this guide walks you through the exact settings to turn it on and connect securely from anywhere. Securely configure remote support tools (rdp, teamviewer, anydesk): auth, encryption, least privilege, session handling, and audit best practices.
Comments are closed.