11 3 4 Implement Intrusion Detection And Prevention Implement
Intrusion Detection Prevention Systems The Ultimate Guide Datasilk Test your knowledge with a quiz created from a student notes for applied computer security net 166. what is the primary function of an intrusion prevention system. In an effort to protect your network from security threats and hackers, you have added snort to pfsense. with snort already installed, you need to configure rules and settings and then assign snort.
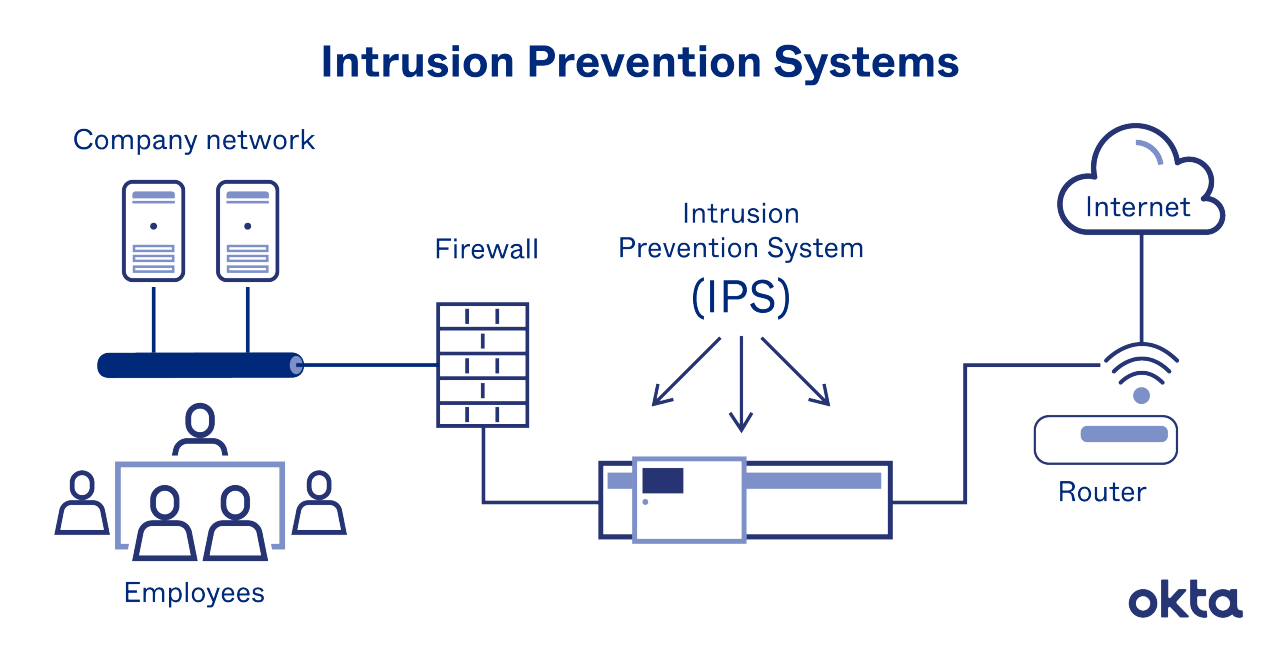
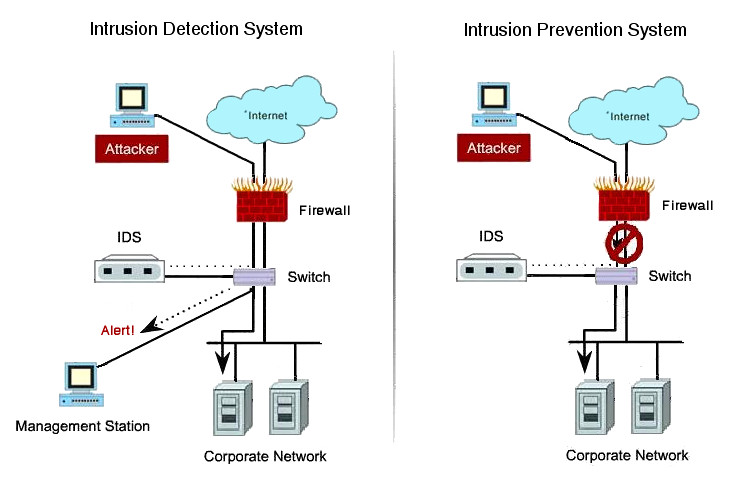
Intrusion Prevention System What Is An Ips How Do They Work Okta Identifying critical assets: begin by identifying the critical assets within your network. these could include servers containing sensitive data, customer information databases, or proprietary. This publication seeks to assist organizations in understanding intrusion detection system (ids) and intrusion prevention system (ips) technologies and in designing, implementing, configuring, securing, monitoring, and maintaining intrusion detection and prevention systems (idps). An intrusion detection system (ids) is a security tool that monitors network traffic or system activities to detect unauthorized access or suspicious behavior. think of it as a "watchdog" that looks for signs of cyber attacks or security breaches, helping administrators respond quickly before damage occurs. The best intrusion prevention system for your business is one that neutralizes cyberthreats before they enter your network. learn how to implement one here.
_.png)
Intrusion Detection System Examples Intrusion Detection System An intrusion detection system (ids) is a security tool that monitors network traffic or system activities to detect unauthorized access or suspicious behavior. think of it as a "watchdog" that looks for signs of cyber attacks or security breaches, helping administrators respond quickly before damage occurs. The best intrusion prevention system for your business is one that neutralizes cyberthreats before they enter your network. learn how to implement one here. An intrusion detection and prevention system (idps) based on signatures is an important security solution that helps to identify known cyber threats by comparing network data to a predetermined list of known indicators of compromise. Tuning is the most important part of intrusion detection deployment the data reduction that results from proper tuning is essential for a fully functional system. View 11.3.5 implement intrusion prevention.rtf from cis 280 at gadsden state community college. 11.3.5 implement intrusion prevention your performance your score: 4 of 5 (80%) pass status: not. Study with quizlet and memorize flashcards containing terms like 11.3.5 implement intrusion prevention, 11.4.7 scan for windows vulnerabilities, 11.4.8 scan for linux vulnerabilities and more.

Intrusion Detection And Prevention System Pptx An intrusion detection and prevention system (idps) based on signatures is an important security solution that helps to identify known cyber threats by comparing network data to a predetermined list of known indicators of compromise. Tuning is the most important part of intrusion detection deployment the data reduction that results from proper tuning is essential for a fully functional system. View 11.3.5 implement intrusion prevention.rtf from cis 280 at gadsden state community college. 11.3.5 implement intrusion prevention your performance your score: 4 of 5 (80%) pass status: not. Study with quizlet and memorize flashcards containing terms like 11.3.5 implement intrusion prevention, 11.4.7 scan for windows vulnerabilities, 11.4.8 scan for linux vulnerabilities and more.
Idps Solutions Boost Firewall Security Telco Ict View 11.3.5 implement intrusion prevention.rtf from cis 280 at gadsden state community college. 11.3.5 implement intrusion prevention your performance your score: 4 of 5 (80%) pass status: not. Study with quizlet and memorize flashcards containing terms like 11.3.5 implement intrusion prevention, 11.4.7 scan for windows vulnerabilities, 11.4.8 scan for linux vulnerabilities and more.
Comments are closed.