10kstudents Basic Buffer Overflows

Lab 1 Buffer Overflow New Download Free Pdf Computer Programming Part i basic buffer overflows (everyone) [pptx] [pdf] [ ] [questions] part ii real buffer overflows (computer scientists) [pptx] [pdf] [ ] [questions]. 10kstudents.eu.
Ppt Buffer Overflows Powerpoint Presentation Free Download Id 5772474 Learn buffer overflow basics: exploitation, prevention, and hands on examples for beginners in cybersecurity and ethical hacking. By demonstrating a buffer overflow attack, we can gain valuable knowledge about vulnerable functions in programming languages and techniques for preventing such vulnerabilities. Please note that this room does not teach buffer overflows from scratch. it is intended to help oscp students and also bring to their attention some features of mona which will save time in the oscp exam. A practical guide to binary exploitation techniques in ctf competitions: stack buffer overflows, ret2win, format string attacks, heap exploitation, and aslr pie bypass with picoctf challenge links for each technique.
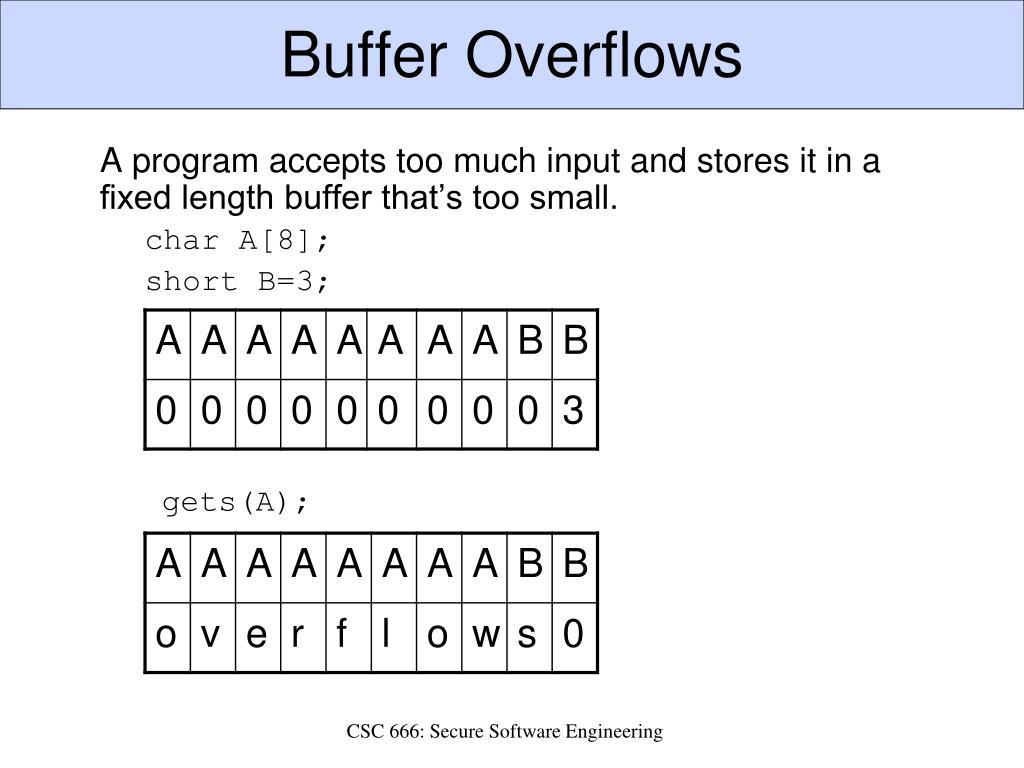
Ppt Buffer Overflows Powerpoint Presentation Free Download Id 2533529 Please note that this room does not teach buffer overflows from scratch. it is intended to help oscp students and also bring to their attention some features of mona which will save time in the oscp exam. A practical guide to binary exploitation techniques in ctf competitions: stack buffer overflows, ret2win, format string attacks, heap exploitation, and aslr pie bypass with picoctf challenge links for each technique. Today, we dove into the basics of buffer overflows, starting with a straightforward example. we explored how memory is organized on the stack and how understanding this layout can help us craft clever exploits. A buffer is a temporary area for data storage. when more data (than was originally allocated to be stored) gets placed by a program or system process, the extra data overflows. it causes some of that data to leak out into other buffers, which can corrupt or overwrite whatever data they were holding. Learn how to get started with basic buffer overflows! in this room, we aim to explore simple stack buffer overflows (without any mitigation’s) on x86 64 linux programs. This article provides a hands on guide to exploiting a buffer overflow, one of the most well known and impactful software vulnerabilities. you'll learn how an attacker can manipulate a program's memory to execute arbitrary code, bypassing its intended behavior.
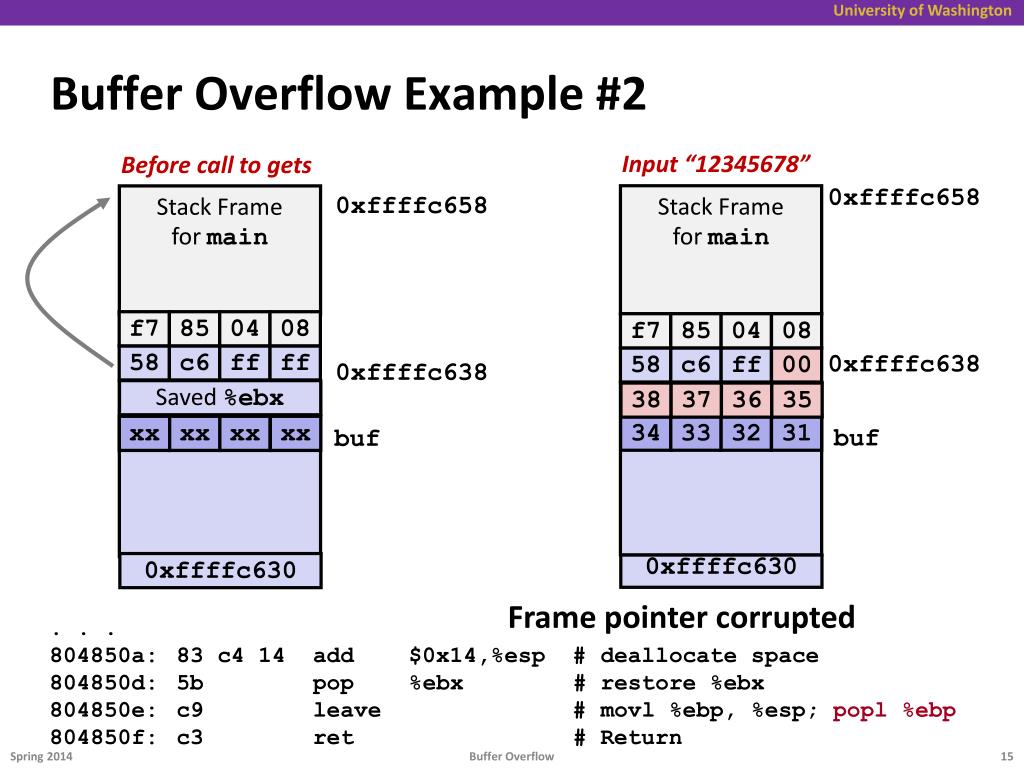
Ppt Buffer Overflows Powerpoint Presentation Free Download Id 5772474 Today, we dove into the basics of buffer overflows, starting with a straightforward example. we explored how memory is organized on the stack and how understanding this layout can help us craft clever exploits. A buffer is a temporary area for data storage. when more data (than was originally allocated to be stored) gets placed by a program or system process, the extra data overflows. it causes some of that data to leak out into other buffers, which can corrupt or overwrite whatever data they were holding. Learn how to get started with basic buffer overflows! in this room, we aim to explore simple stack buffer overflows (without any mitigation’s) on x86 64 linux programs. This article provides a hands on guide to exploiting a buffer overflow, one of the most well known and impactful software vulnerabilities. you'll learn how an attacker can manipulate a program's memory to execute arbitrary code, bypassing its intended behavior.
.png?width=1800&height=1200&name=Blog - Understanding%2c detecting%2c and fixing buffer overflows (header).png)
Everything About Buffer Overflows Blog Code Intelligence Learn how to get started with basic buffer overflows! in this room, we aim to explore simple stack buffer overflows (without any mitigation’s) on x86 64 linux programs. This article provides a hands on guide to exploiting a buffer overflow, one of the most well known and impactful software vulnerabilities. you'll learn how an attacker can manipulate a program's memory to execute arbitrary code, bypassing its intended behavior.
Comments are closed.