08 Security Pdf Cloud Computing Computer Security

Security In Cloud Computing Pdf Information Security Cloud Computing Identify and assess key cybersecurity threats in cloud computing. examine the unique challenges in cloud security. explore mitigation strategies and future security trends. This paper gives a better understanding on the concept of cloud computing and the risks that came up after outsourcing data handling tasks.

Cloud Security Pdf Cloud Computing Computer Security This review paper critically examines ten state of the art research papers on security and privacy in cloud computing. it identifies key issues, methodologies adopted to solve them, and evaluates the proposed solutions. Introduction to cloud computing security computing and how its security evolved. we will learn how serverless computing relates to cloud computing and how securing serverless computing differs from th typical cloud computing cybersecurity. we will review cybersecurity, how it applies. It explores the primary security risks associated with cloud adoption, such as data breaches, loss of control, and unauthorized access. the study also examines the regulatory. protection laws. the paper concludes by highlighting the evolving nature of cloud security and the need for. Shared computing resources change the threat landscape. sharing a system with a vulnerable application may result in those shared resources becoming compromised and consequently spreading attacks to your applications.
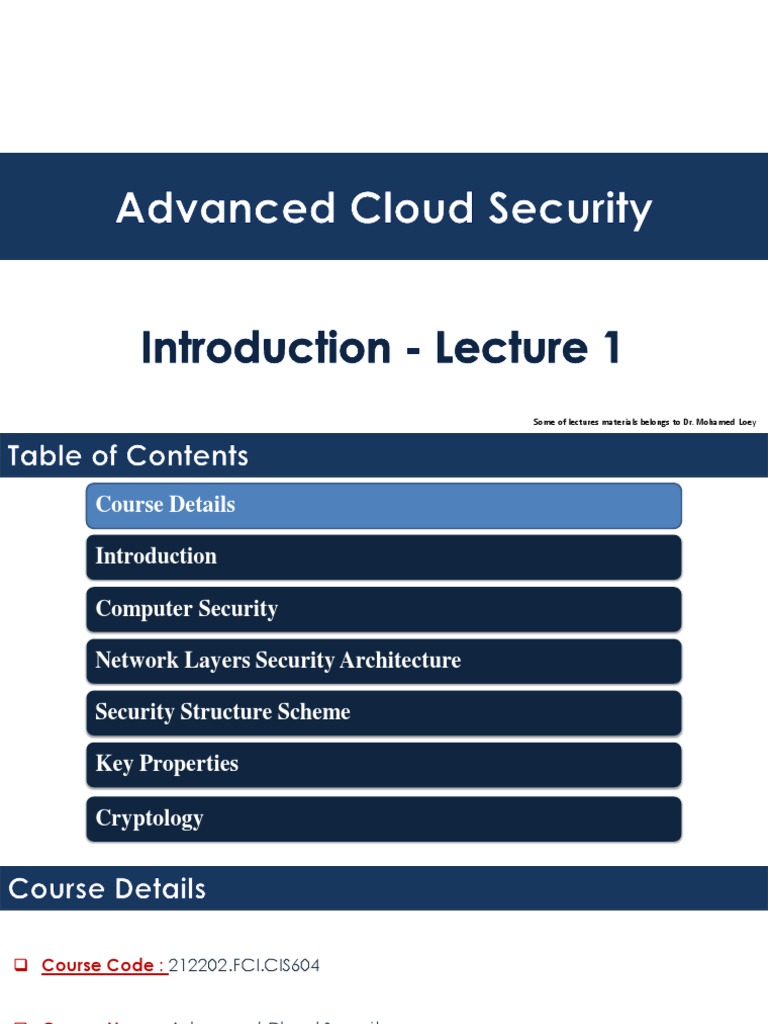
Cloud Security Lecture 1 Pdf Cryptography Encryption It explores the primary security risks associated with cloud adoption, such as data breaches, loss of control, and unauthorized access. the study also examines the regulatory. protection laws. the paper concludes by highlighting the evolving nature of cloud security and the need for. Shared computing resources change the threat landscape. sharing a system with a vulnerable application may result in those shared resources becoming compromised and consequently spreading attacks to your applications. This handbook offers a comprehensive overview of cloud computing security technology and implementation, while exploring practical solutions to a wide range of cloud computing security issues. The key to secure use of cloud computing is a clear, shared understanding of the division of security responsibilities between the pro vider and client, and the ability to verify that both are meeting their responsibilities. This paper explores the key security issues and privacy concerns associated with cloud computing, including the loss of control over sensitive data, unauthorized access, data integrity, and compliance with regulations. This publication is designed to provide executives from organisations looking to utilise cloud computing services an overview of the components that make up ‘cloud’ and help understand the security risks to be considered when using cloud computing.
Comments are closed.