04 Role Based Access Control Pdf Business

Role Based Access Control Pdf Systems Engineering Computer Data It explores the fundamental concepts of rbac, including its core principle of assigning access rights based on organizational roles rather than individual users. the article delves into the. 04 role based access control free download as powerpoint presentation (.ppt .pptx), pdf file (.pdf), text file (.txt) or view presentation slides online.

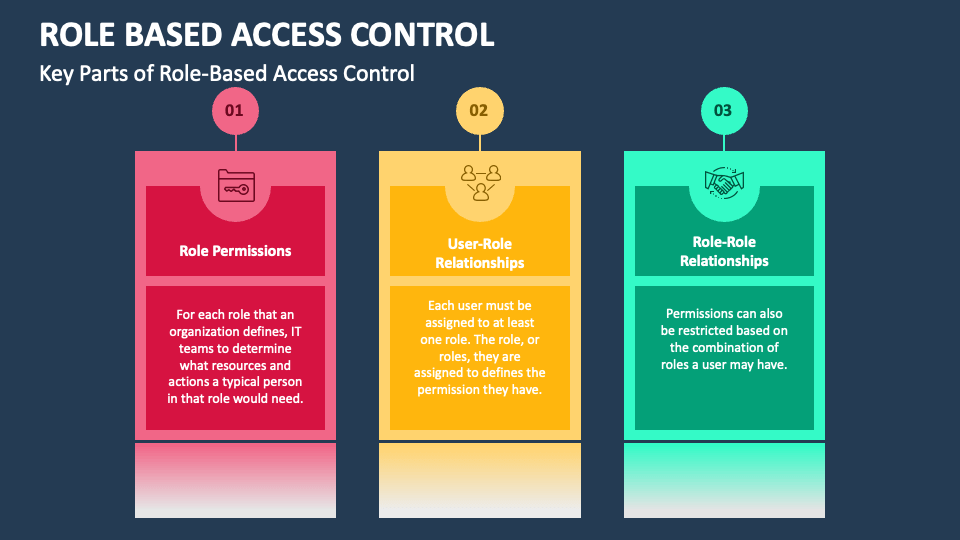
Role Based Access Control Rbac Icon Access Control Brochure Pdf In today’s iam systems for large enterprises, one of the most important components for turning resource access is rbac, which is short for role based access control. Rating the principles we used in developing it; we give complete speci ̄cation of hierarchical rbac, with an ad ditional option for managing the relationship on roles; we describe a speci ̄cation of constrained rbac, maki. Role based access control, or rbac for short, is an approach to restrict system access to authorized users. it aims to ensure the confidentiality, integrity, and availability of information since, based on the principle of least privilege, it restricts users' access and the actions they can perform. Rbac enhances security by enforcing the principle of least privilege for sensitive information access. efficient management of user roles reduces administrative burdens and streamlines access control processes. the study evaluates best practices for implementing rbac in large scale enterprises.

Pdf Role Based Access Control 9781580533249 Role based access control, or rbac for short, is an approach to restrict system access to authorized users. it aims to ensure the confidentiality, integrity, and availability of information since, based on the principle of least privilege, it restricts users' access and the actions they can perform. Rbac enhances security by enforcing the principle of least privilege for sensitive information access. efficient management of user roles reduces administrative burdens and streamlines access control processes. the study evaluates best practices for implementing rbac in large scale enterprises. Role based access control (rabc) ss control or role based security. role based access control assigns specific rules or policies to individual users or groups of use. To enable system integrators to integrate rbac into the various it infrastructures found in an enterprise like web applications, such as java and federated database systems, the book provides an analysis of research ideas and prototypes built so far. In this article, we present some of the business benefits of managing access rights via roles, discuss whether or not roles are right for you, and provide guidance for deploying role based access controls. Roles are engineered based on the principle of least privileged . a role contains the minimum amount of permissions to instantiate an object. a user is assigned to a role that allows him or her to perform only what’s required for that role. no single role is given more permission than the same role for another user.
Pdf Role Based Access Control Second Edition 9781596931145 Role based access control (rabc) ss control or role based security. role based access control assigns specific rules or policies to individual users or groups of use. To enable system integrators to integrate rbac into the various it infrastructures found in an enterprise like web applications, such as java and federated database systems, the book provides an analysis of research ideas and prototypes built so far. In this article, we present some of the business benefits of managing access rights via roles, discuss whether or not roles are right for you, and provide guidance for deploying role based access controls. Roles are engineered based on the principle of least privileged . a role contains the minimum amount of permissions to instantiate an object. a user is assigned to a role that allows him or her to perform only what’s required for that role. no single role is given more permission than the same role for another user.

04 Role Based Access Control Pdf Business In this article, we present some of the business benefits of managing access rights via roles, discuss whether or not roles are right for you, and provide guidance for deploying role based access controls. Roles are engineered based on the principle of least privileged . a role contains the minimum amount of permissions to instantiate an object. a user is assigned to a role that allows him or her to perform only what’s required for that role. no single role is given more permission than the same role for another user.
Role Based Access Control Powerpoint And Google Slides Template Ppt
Comments are closed.