02 Exploring The Reverse Shell Source Code And Api Breakdown

Reverse Shell1 Pdf Port Computer Networking Security Hacker Perfect for cybersecurity enthusiasts and coders eager to understand the mechanics behind a windows reverse shell. follow along to see the code in action!. 🏗️ you can’t create reliable windows shellcode without a precise understanding of the windows api. this goes far beyond just knowing which function to call.
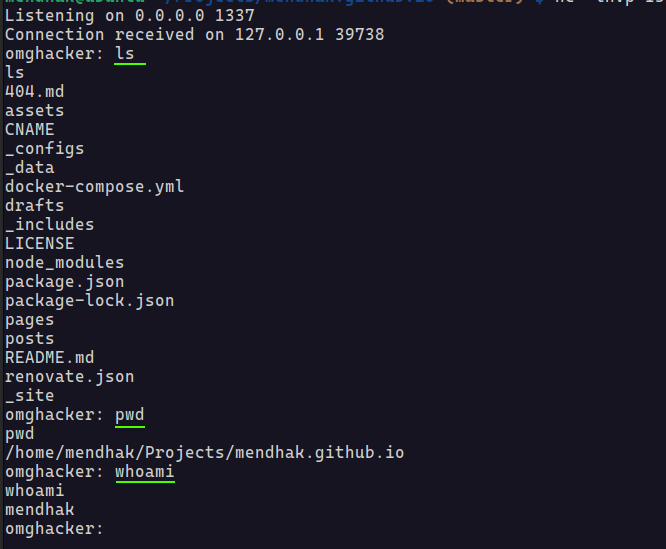
What Does A Reverse Shell Actually Look Like This playlist builds on the creating windows shellcode and understanding runtime linking series, guiding you through crafting a reverse shell on windows. Here i host free cybersecurity educational content focused on malware analysis, reverse engineering and ethical hacking. where in the world is printf? using the legacy library file to link with. Introduction to malware binary triage (imbt) course looking to level up your skills? get 10% off using coupon code: mwnews10 for any flavor. enroll now and save 10%: coupon code mwnews10. The first step is to develop a function to locate the address of kernel32.dll , a dll which contains several windows api functions that are needed throughout the code.
Github Prebenb01 Reverse Shell Introduction to malware binary triage (imbt) course looking to level up your skills? get 10% off using coupon code: mwnews10 for any flavor. enroll now and save 10%: coupon code mwnews10. The first step is to develop a function to locate the address of kernel32.dll , a dll which contains several windows api functions that are needed throughout the code. This document covers the reverse shell implementation located in the basic concepts directory, which demonstrates a fundamental offensive security technique for educational purposes. A list of useful payloads and bypass for web application security and pentest ctf payloadsallthethings methodology and resources reverse shell cheatsheet.md at master · swisskyrepo payloadsallthethings. In this article we are going to be implementing the windows reverse shell and learning all there is to know about the reverse shells. This page deals with the former. your options for creating a reverse shell are limited by the scripting languages installed on the target system – though you could probably upload a binary program too if you’re suitably well prepared. the examples shown are tailored to unix like systems.
Comments are closed.