01 Cybercrime Flowchart Pdf
Free Flowchart Templates Editable And Downloadable 01 cybercrime flowchart free download as pdf file (.pdf) or read online for free. Undergraduate cyber criminology flowchart this document should not be considered a complete representation of all degree requirements at fsu. arrows indicate prerequisite – “co” indicates co requisite (the classes may be taken simultaneously).

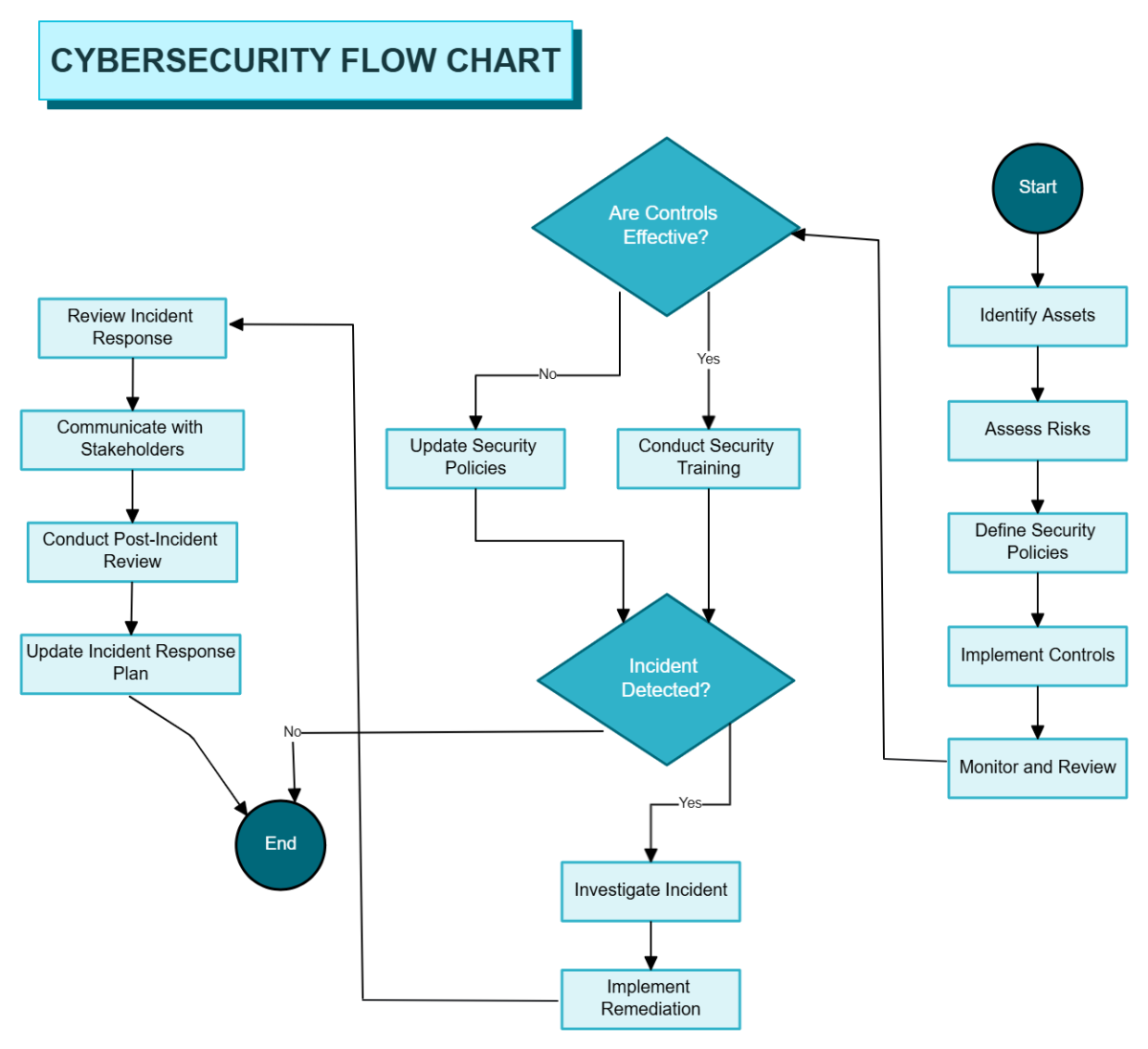
Proposed Flowchart For Cyber Attack Detection Download Scientific Diagram Tracing cybercrime's timeline provides vital context to catalyze preemptive actions against potential attacks in an increasingly interconnected online ecosystem. Ule series on cybercrime. the full range of e4j materials includes university modules on integrity and ethics, crime prevention and criminal justice, anti corruption, organized crime, firearms, trafficking in persons smuggling of migrants, wildlife, forest and fisheries crime, counter terror. Download pdf flow chart on basic steps on investigating cybercrime [9n0kvm90154v]. A cybercrime strategy defines the necessary steps to take to institute good corporate data governance and personal cyber hygiene in order to limit economic impact.

Ping Flowchart Sederhana Tentang Cyber Law Computer Crime Act Dan Download pdf flow chart on basic steps on investigating cybercrime [9n0kvm90154v]. A cybercrime strategy defines the necessary steps to take to institute good corporate data governance and personal cyber hygiene in order to limit economic impact. Undergraduate cyber criminology flowchart 2024 students must earn a “c” or better in ccj 2020, ccj 3011, ccj 4700 and ccj 4746 and a grade of “c ” or better in all other courses that count toward the major. You can export it as a pdf for high quality printouts. This document outlines the basic 12 steps for investigating cybercrime cases: 1. interview the complainant and determine if the complaint falls under relevant cybercrime laws. In partnership with detica to look more closely at the cost of cybercrime and to gain a better appreciation of the costs to the uk economy of intellectual property (ip) theft and industrial espionage.
Comments are closed.