%f0%9f%9a%a8 Vite Development Server Arbitrary File Read Bypass Cve 2025 30208 Explained

Vite Development Server File Read Bypass Cve 2025 30208 Discover cve 2025 30208, a critical arbitrary file read vulnerability in the vite development server. learn how remote attackers exploit @fs url handling to access sensitive files. Only apps explicitly exposing the vite dev server to the network (using ` host` or `server.host` config option) are affected. versions 6.2.3, 6.1.2, 6.0.12, 5.4.15, and 4.5.10 fix the issue. nvd enrichment efforts reference publicly available information to associate vector strings.

Vite Development Server File Read Bypass Cve 2025 30208 A poc of the exploit script for the arbitrary file read vulnerability of vite @fs path traversal in transformmiddleware (cve 2025 30208). detailed analysis can be refer to this post. Cve 2025 30208 lets anyone bypass vite’s file access restrictions using a simple url trick. attackers can read basically any file on the server, as long as the dev server is exposed to the network. The vulnerability allows an attacker to read arbitrary files on the server’s filesystem by bypassing the server.fs.deny protection. first, try to access etc passwd using the standard @fs prefix to verify that normal access to files outside the allowed directories is properly blocked:. What happened? in march 2025, vite maintainers released security patches to fix an arbitrary file read vulnerability. the flaw allows attackers to bypass vite's file access restrictions using crafted urls, reading sensitive files from the host server.
Vite Arbitrary File Read Vulnerability Cve 2025 30208 Nsfocus Inc The vulnerability allows an attacker to read arbitrary files on the server’s filesystem by bypassing the server.fs.deny protection. first, try to access etc passwd using the standard @fs prefix to verify that normal access to files outside the allowed directories is properly blocked:. What happened? in march 2025, vite maintainers released security patches to fix an arbitrary file read vulnerability. the flaw allows attackers to bypass vite's file access restrictions using crafted urls, reading sensitive files from the host server. Cve 2025 30208 is a vite dev server flaw that allows file access bypass via query manipulation. learn impact, risks, and recommended mitigations. The contents of arbitrary files can be returned to the browser. only apps explicitly exposing the vite dev server to the network (using ` host` or `server.host` config option) are affected. Normally, the `@fs` mechanism restricts access to files outside the project’s serving allow list. by appending specially crafted query parameters like `?raw??` or `?import&raw??` to the url, an attacker can bypass these file access restrictions. Since the vite development server does not strictly verify the path when processing url requests, unauthenticated attackers can bypass path access restrictions by constructing special urls to obtain sensitive files outside the project root directory.
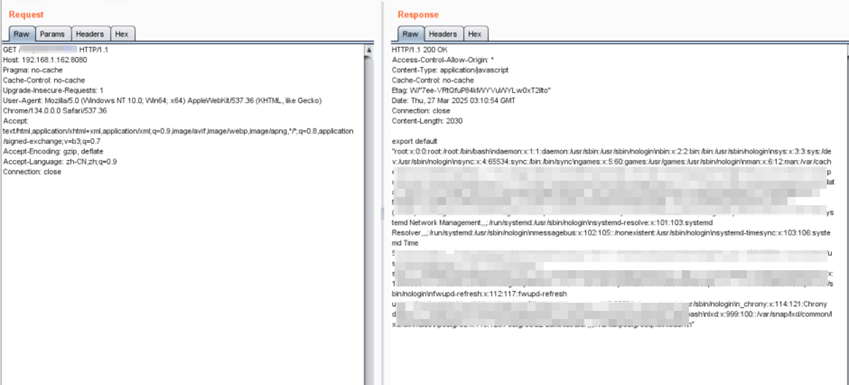
Vite Arbitrary File Read Vulnerability Cve 2025 30208 Nsfocus Inc Cve 2025 30208 is a vite dev server flaw that allows file access bypass via query manipulation. learn impact, risks, and recommended mitigations. The contents of arbitrary files can be returned to the browser. only apps explicitly exposing the vite dev server to the network (using ` host` or `server.host` config option) are affected. Normally, the `@fs` mechanism restricts access to files outside the project’s serving allow list. by appending specially crafted query parameters like `?raw??` or `?import&raw??` to the url, an attacker can bypass these file access restrictions. Since the vite development server does not strictly verify the path when processing url requests, unauthenticated attackers can bypass path access restrictions by constructing special urls to obtain sensitive files outside the project root directory.
Comments are closed.