%e9%80%82%e7%94%a8%e4%ba%8e Azure Devops %e7%9a%84 Github Advanced Security %e7%9a%84%e8%ae%a1%e8%b4%b9 Azure Repos
Security Overview On Github Advanced Security For Azure Devops Azure Yandex finds anything: webpages, images, music, good. solve any problem — from everyday to a scientific one. search by text, voice or image. Fast and easy mac address lookup on ieee directory and wireshark manufacturer database. search vendor, manufacturer or organization of a device by mac oui address. fast rest api.
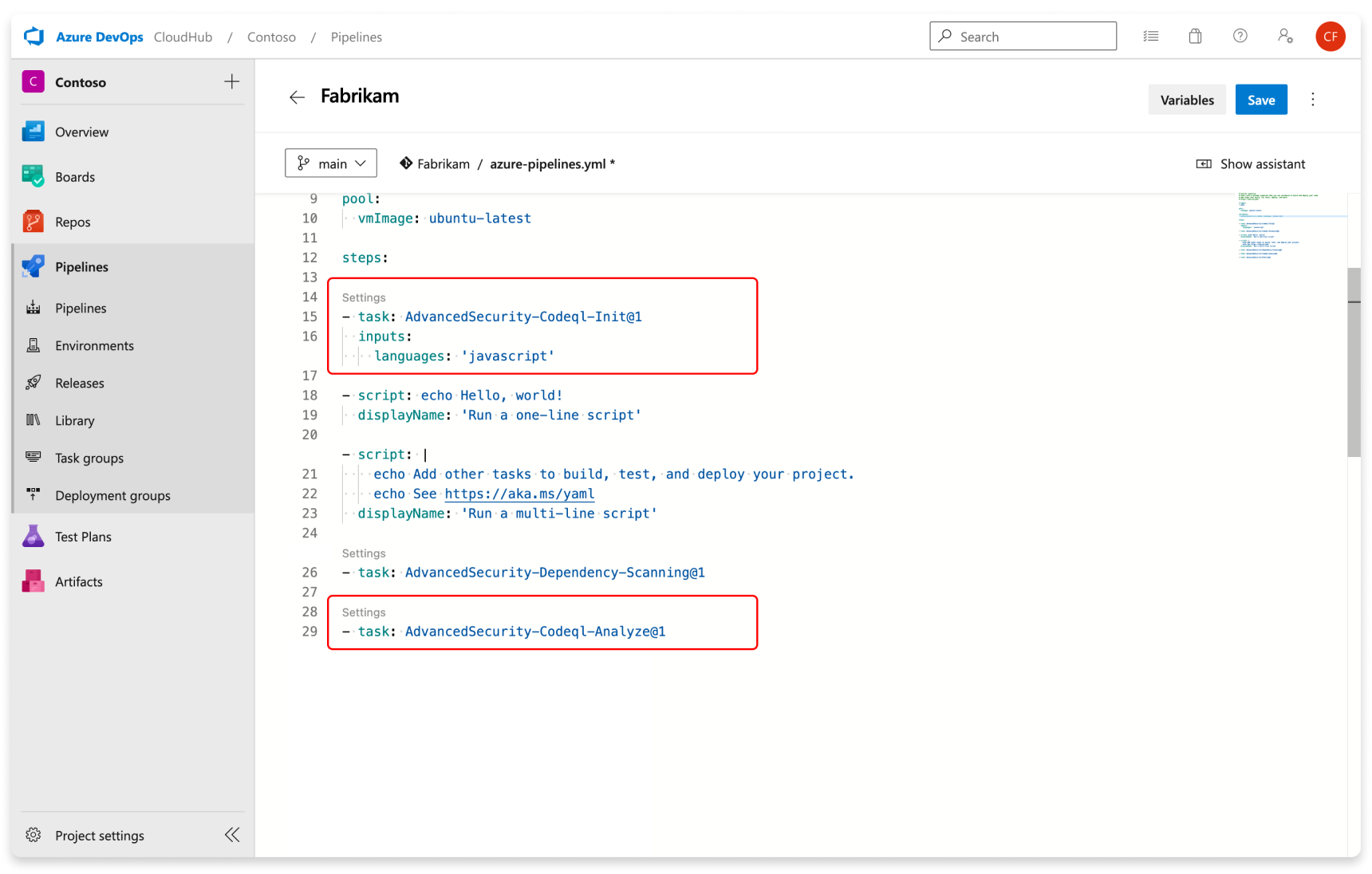
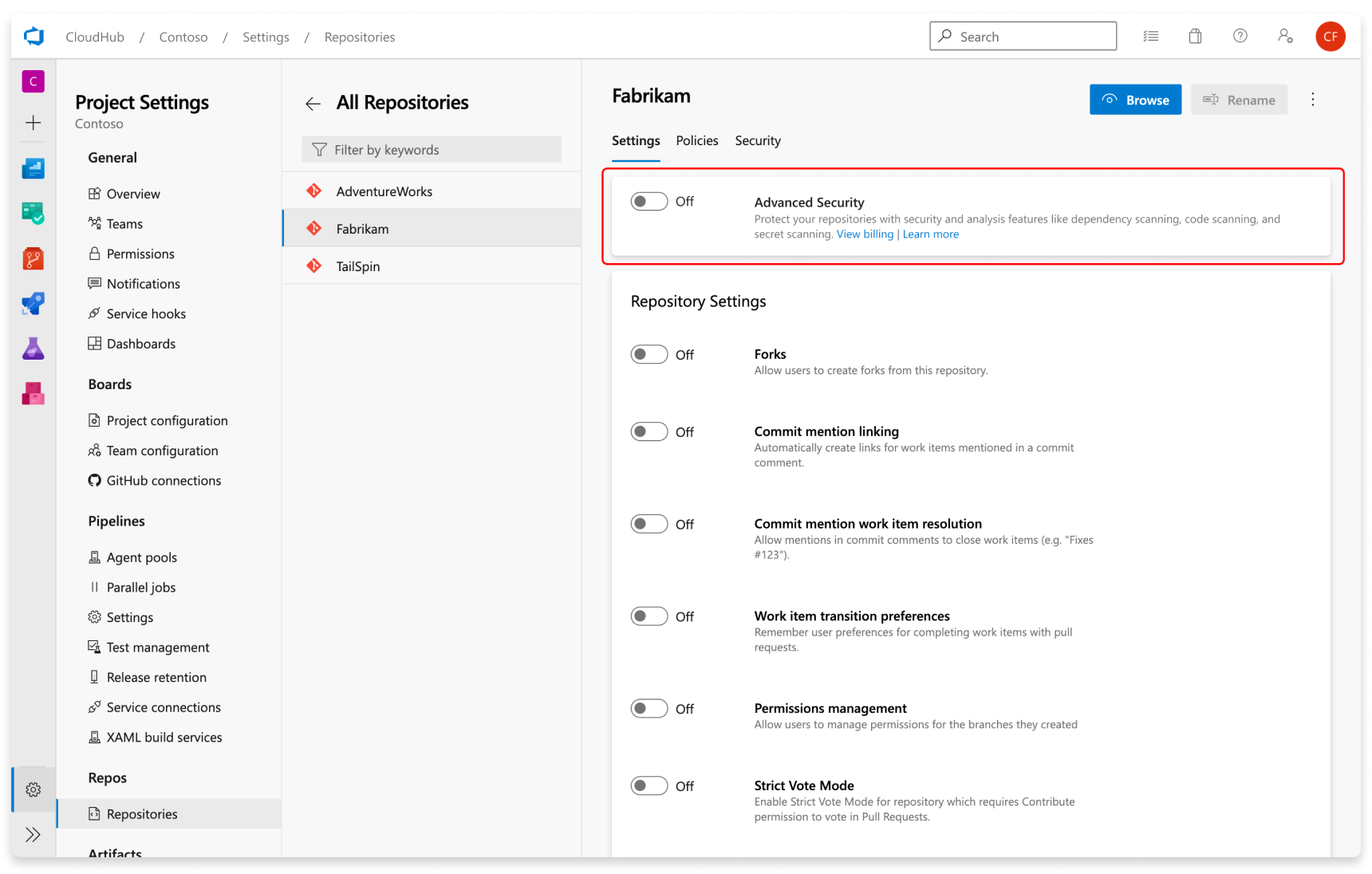
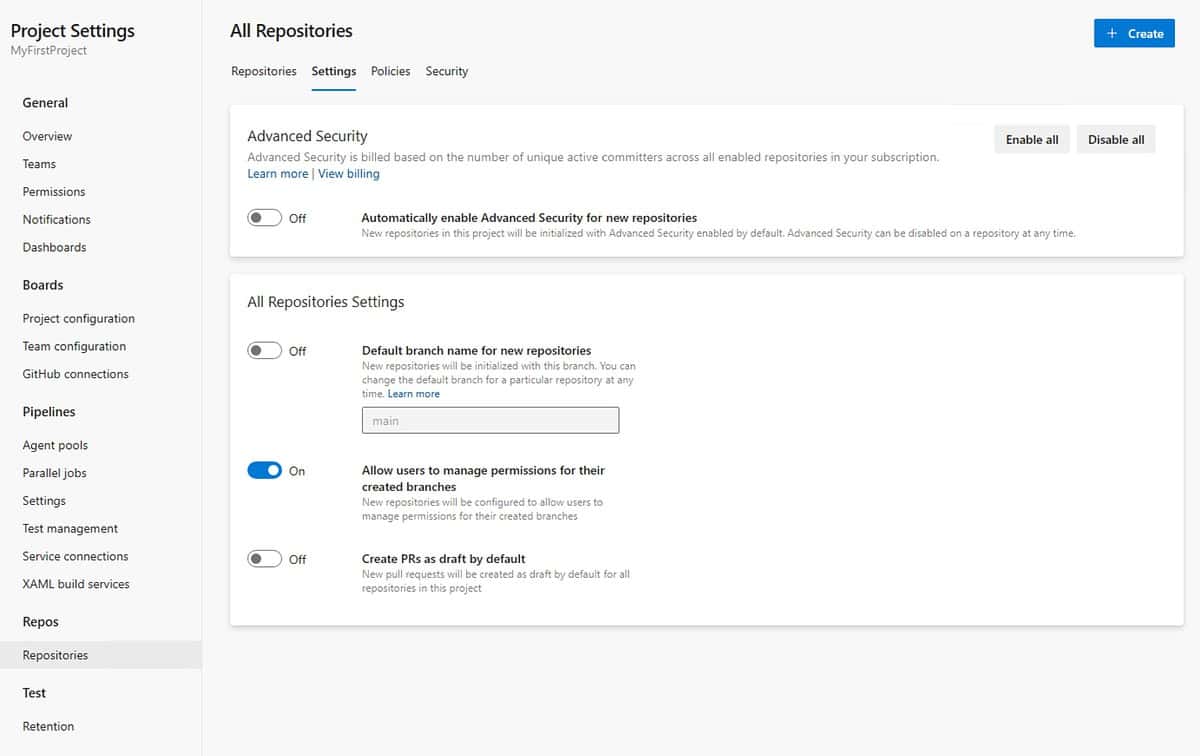
Configure Github Advanced Security For Azure Devops Features Azure Search the world's information, including webpages, images, videos and more. google has many special features to help you find exactly what you're looking for. It is an acronym for uniform resource locator. a url is an address that browsers probe in order to connect to a web server. two example url's could be: url's strictly use the ascii character set to send data across the internet. they, therefore, must be encoded before being sent. At a press briefing on wednesday, us air force gen. dan caine, chairman of the joint chiefs of staff, shared updated numbers from operation epic fury, the us' military campaign against iran. caine said the us forces and gulf state partners and allies had collectively struck more than 13,000 targets in iran. This paper proposes a framework of digital models integrating spatial narrative theories to represent the narrative and narrative of experience of a chinese classic novel, the tale of li wa, which has been diversely interpreted by literature and historians in the past approximately 900 years.
Microsoft Announces The General Availability Of Github Advanced At a press briefing on wednesday, us air force gen. dan caine, chairman of the joint chiefs of staff, shared updated numbers from operation epic fury, the us' military campaign against iran. caine said the us forces and gulf state partners and allies had collectively struck more than 13,000 targets in iran. This paper proposes a framework of digital models integrating spatial narrative theories to represent the narrative and narrative of experience of a chinese classic novel, the tale of li wa, which has been diversely interpreted by literature and historians in the past approximately 900 years. With this process, you can find all the different mac address block prefixes that are used by a particular company. this mac address vendor lookup can be useful if an admin wants to grant network access to a wide range of mac address blocks belonging to a particular company. Url encoding converts characters into a format that can be transmitted over the internet. urls can only be sent over the internet using the ascii character set. since urls often contain characters outside the ascii set, the url has to be converted into a valid ascii format. Bilibili search , southeast asia\'s leading anime, comics, and games (acg) community where people can create, watch and share engaging videos. Identifying unknown devices on your network is crucial for security. if you see an unfamiliar mac address connecting to your network, looking up its manufacturer can help determine if it is a legitimate device or a potential security threat.
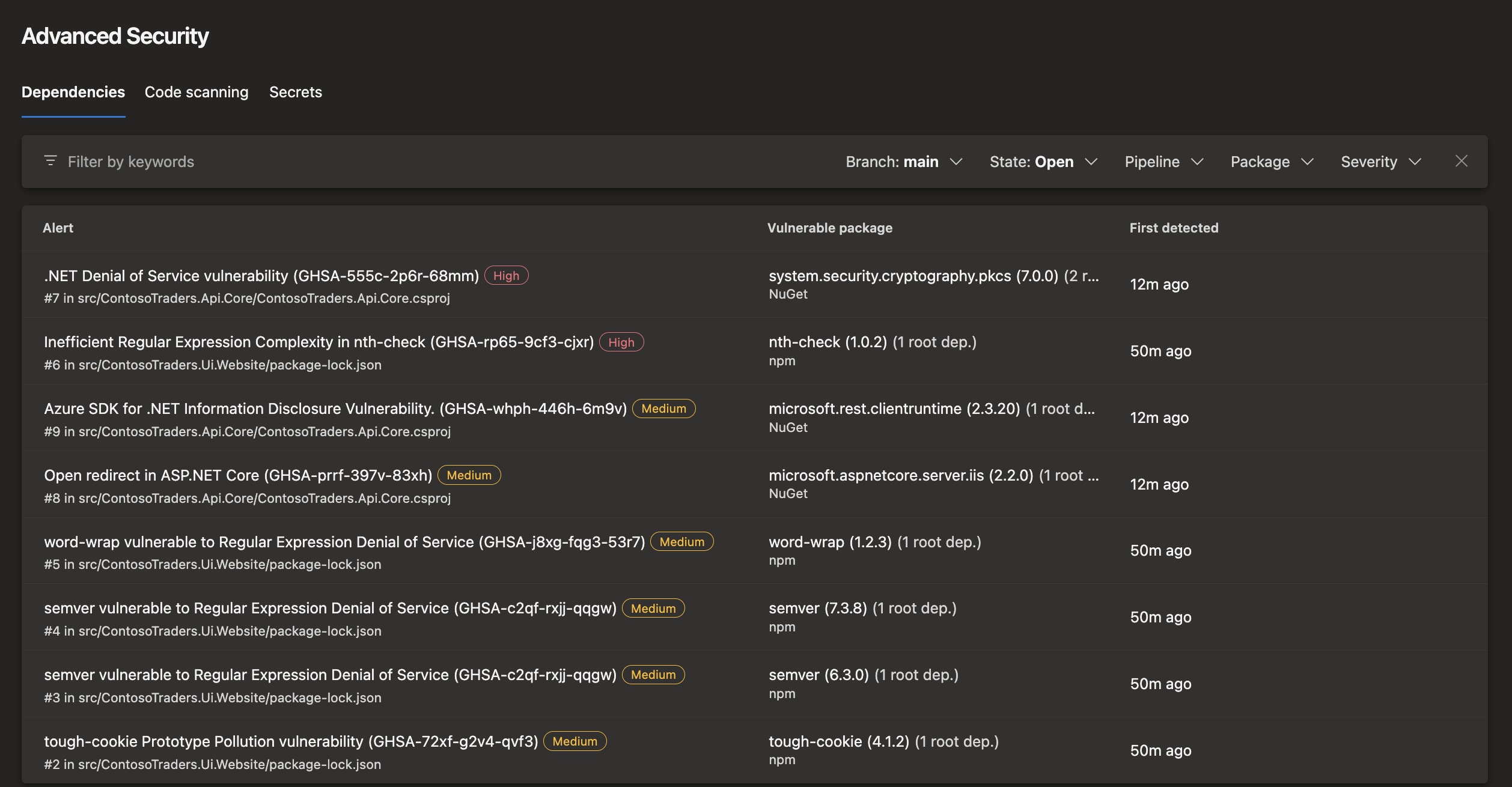
Github Advanced Security For Azure Devops Nicholas Chang With this process, you can find all the different mac address block prefixes that are used by a particular company. this mac address vendor lookup can be useful if an admin wants to grant network access to a wide range of mac address blocks belonging to a particular company. Url encoding converts characters into a format that can be transmitted over the internet. urls can only be sent over the internet using the ascii character set. since urls often contain characters outside the ascii set, the url has to be converted into a valid ascii format. Bilibili search , southeast asia\'s leading anime, comics, and games (acg) community where people can create, watch and share engaging videos. Identifying unknown devices on your network is crucial for security. if you see an unfamiliar mac address connecting to your network, looking up its manufacturer can help determine if it is a legitimate device or a potential security threat.

Github Advanced Security For Azure Devops Now Available Alta Ict Bilibili search , southeast asia\'s leading anime, comics, and games (acg) community where people can create, watch and share engaging videos. Identifying unknown devices on your network is crucial for security. if you see an unfamiliar mac address connecting to your network, looking up its manufacturer can help determine if it is a legitimate device or a potential security threat.
Comments are closed.