%d0%b1%d2%91 %d0%b1%d2%91 %d0%b1%d2%91 %d0%ba%d1%9a%d0%b9%d2%91%d0%b1%d2%91%d1%9f %d0%b1%d2%91 %d0%b1%d2%91 %d0%ba%d1%9a %d0%b9%d1%94%d0%b9%d1%9e%d0%b9%d2%91%d0%ba%d1%9a Techno Designs %d0%b2%d1%92

D2 B0 D0 Bb D1 82 D1 82 D1 8b D2 9b D0 Bc D0 B5 D0 Bc D0 Bb D0 B5 D0 Search the world's information, including webpages, images, videos and more. google has many special features to help you find exactly what you're looking for. © 2026 google llc.

мягенькая клавиатура Kiiboom Phantom 68 Youtube Oui ma l organization company id organization address 28 6f b9 (hex) nokia. 🔑 detects compromised employee and consumer credentials. 🌑 scans the dark web for cyber threats targeting your company. 🛡 monitors your digital attack surface for external vulnerabilities. what does it do? maclookup provides an easy way to search for mac address prefixes and matches them to the chipset's manufacturer. Giacomo cimberio s.p.a. 8c:c8:f4|ieee registration authority f4:83:e1|shanghai clouder semiconductor co.,ltd 08:3e:5d|sagemcom broadband sas 3c:bd:3e|beijing xiaomi electronics co., ltd. a0:84:cb|sonicsensory,inc. d4:7a:e2|samsung electronics co.,ltd 68:54:fd|amazon technologies inc. 00:03:bc|cot gmbh e4:47:90|guangdong oppo mobile telecommunications corp.,ltd 38:45:4c|light labs, inc. 00:0a:49|f5 networks, inc. 00:a0:c8|adtran inc f4:96:51|nakayo inc 44:62:46|comat ag 34:fc:b9|hewlett packard enterprise 70:91:8f|weber stephen products llc d8:e0:e1|samsung electronics co.,ltd 7c:10:15|brilliant home technology, inc. d8:c7:71|huawei technologies co.,ltd e0:2a:82|universal global scientific industrial co., ltd. b0:f9:63|hangzhou h3c technologies co., limited a8:40:41|dragino technology co., limited e0:22:02|arris group, inc. d8:25:b0|rockeetech systems co.,ltd. 74:61:4b|chongqing huijiatong information technology co., ltd. 98:d2:93|google, inc. cc:b8:a8|ampak technology, inc. 10:77:b0|fiberhome telecommunication. The main core of question is — i did not know what's the name of this type of string. i am getting output function strings in this format %d0%9f%d1%80%d0%b8%d0%b2%d0%b5%d1%82. i don't know what typ.
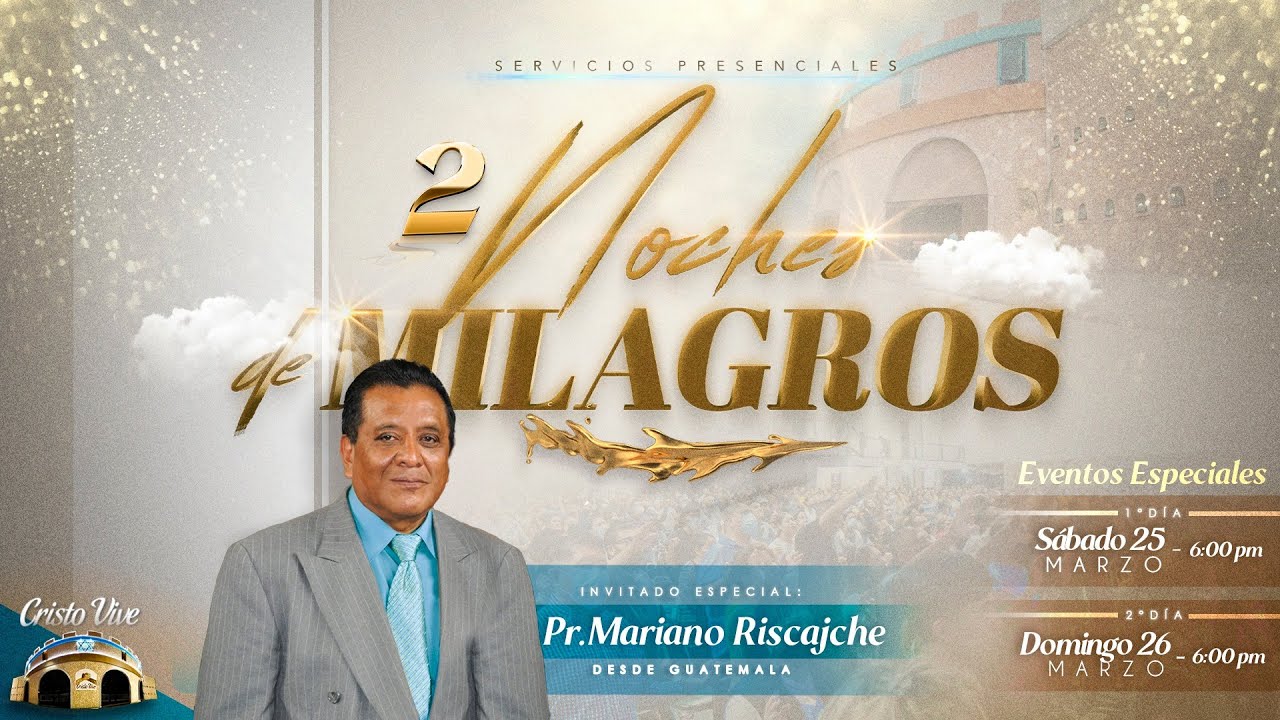
рџ џрџџ Noches De Milagros Con El Pastor Mariano Riscajche рџ рџ Youtube Giacomo cimberio s.p.a. 8c:c8:f4|ieee registration authority f4:83:e1|shanghai clouder semiconductor co.,ltd 08:3e:5d|sagemcom broadband sas 3c:bd:3e|beijing xiaomi electronics co., ltd. a0:84:cb|sonicsensory,inc. d4:7a:e2|samsung electronics co.,ltd 68:54:fd|amazon technologies inc. 00:03:bc|cot gmbh e4:47:90|guangdong oppo mobile telecommunications corp.,ltd 38:45:4c|light labs, inc. 00:0a:49|f5 networks, inc. 00:a0:c8|adtran inc f4:96:51|nakayo inc 44:62:46|comat ag 34:fc:b9|hewlett packard enterprise 70:91:8f|weber stephen products llc d8:e0:e1|samsung electronics co.,ltd 7c:10:15|brilliant home technology, inc. d8:c7:71|huawei technologies co.,ltd e0:2a:82|universal global scientific industrial co., ltd. b0:f9:63|hangzhou h3c technologies co., limited a8:40:41|dragino technology co., limited e0:22:02|arris group, inc. d8:25:b0|rockeetech systems co.,ltd. 74:61:4b|chongqing huijiatong information technology co., ltd. 98:d2:93|google, inc. cc:b8:a8|ampak technology, inc. 10:77:b0|fiberhome telecommunication. The main core of question is — i did not know what's the name of this type of string. i am getting output function strings in this format %d0%9f%d1%80%d0%b8%d0%b2%d0%b5%d1%82. i don't know what typ. # # this is wireshark 'manuf' file, which started out as a subset of michael # patton's list and grew from there. the wireshark list and michael's list # were merged in 2016. # # in the event of data set collisions the wireshark entries have been given # precedence, followed by michael patton's, followed by the ieee. There two steps in which url escape online works. in first step the all characters in the string separated using utf 8 encoding. convert each character that are not ascii letters into hexadecimal values. please check the table below to find out the backend key code against each charset. B2 b3 b3 b3 b3 b3 b3 b3 cc cc cc cc cc dc cc cc e1 e1 e1 e1 e1 e1 e1 e1 10 10 10 10 10 10 10 10 e1 61 e1 e1 e1 e1 e1 e1 a1 a1 a1 a1 a1 a1 a1 a1 d2 d2 f2 d2 d2 d2 d2 d2 89 89 89 89 89 89 89 89 19 19 19 19 19 39 19 19 3f 3f 3f 3f 3f 3f 3f 3f 96 94 94 94 94 94 94 94 5c 5c 5c 5c 5c 5c 5c 5c 20 20 20 20 20 20 20 20 82 80 82 82 82 82 82 82 3e 3e 3e 3e 3e 3e 3e 3e b8 b8 b8 a8 b8 b8 b8 b8 8f 8f 8f 8f 8f 8f 8f 8f 8e 8a 8e 8e 8e 8e 8e 8e 39 39 39 39 39 39 39 39 cb cb cb cb cb cb cb cb b7 b7 b7 b7 b7 b7 b7 b7 40 40 40 40 40 40 40 40 b9 b9 b9 b9 b9 b8 b9 b9 70 70 70 70 70 70 70 70 2f 2b 2b 2b 2b 2b 2b 2b. Url encoding is pretty straight forward, just a percent sign followed by the hexadecimal digits of the byte values corresponding to the codepoints of illegal characters.

Tiflis Soft Tone Minor E2 E3 G3 A3 B3 C4 E4 F G4 A4 B4 C4 E G # # this is wireshark 'manuf' file, which started out as a subset of michael # patton's list and grew from there. the wireshark list and michael's list # were merged in 2016. # # in the event of data set collisions the wireshark entries have been given # precedence, followed by michael patton's, followed by the ieee. There two steps in which url escape online works. in first step the all characters in the string separated using utf 8 encoding. convert each character that are not ascii letters into hexadecimal values. please check the table below to find out the backend key code against each charset. B2 b3 b3 b3 b3 b3 b3 b3 cc cc cc cc cc dc cc cc e1 e1 e1 e1 e1 e1 e1 e1 10 10 10 10 10 10 10 10 e1 61 e1 e1 e1 e1 e1 e1 a1 a1 a1 a1 a1 a1 a1 a1 d2 d2 f2 d2 d2 d2 d2 d2 89 89 89 89 89 89 89 89 19 19 19 19 19 39 19 19 3f 3f 3f 3f 3f 3f 3f 3f 96 94 94 94 94 94 94 94 5c 5c 5c 5c 5c 5c 5c 5c 20 20 20 20 20 20 20 20 82 80 82 82 82 82 82 82 3e 3e 3e 3e 3e 3e 3e 3e b8 b8 b8 a8 b8 b8 b8 b8 8f 8f 8f 8f 8f 8f 8f 8f 8e 8a 8e 8e 8e 8e 8e 8e 39 39 39 39 39 39 39 39 cb cb cb cb cb cb cb cb b7 b7 b7 b7 b7 b7 b7 b7 40 40 40 40 40 40 40 40 b9 b9 b9 b9 b9 b8 b9 b9 70 70 70 70 70 70 70 70 2f 2b 2b 2b 2b 2b 2b 2b. Url encoding is pretty straight forward, just a percent sign followed by the hexadecimal digits of the byte values corresponding to the codepoints of illegal characters.
Comments are closed.